Computer networks are not just responsible for communication, but our entire way of life has evolved. The way we work, the way we interact, among other ways have changed significantly.
Some of the ways we use computer networks include:
- Business – online banking, e-mail, e-commerce.
- Entertainment – online movies, online games.
- Social interactions – instant messaging, social networking sites.
An interconnection of multiple devices, also known as hosts, that are connected using multiple paths for the purpose of sending/receiving data or media. Computer networks can also include multiple devices/mediums which help in the communication between two different devices; these are known as Network devices and include things such as routers, switches, hubs, and bridges.
A computer network is a group of devices connected with each other through a transmission medium such as wires, cables etc. These devices can be computers, printers, scanners, Fax machines etc
A computer network has following features:
Performance: Performance of a computer network is measured in terms of response time. The response time of sending and receiving data from one node (computer in a computer network are often referred as node) to another should be minimal.
Data Sharing: One of the reason why we use a computer network is to share the data between different systems connected with each other through a transmission media.
Backup: A computer network must have a central server that keeps the backup of all the data that is to be shared over a network so that in case of a failure it should be able to recover the data faster.
Software and hardware compatibility: A computer network must not limit all the computers in a computer network to use same software and hardware, instead it should allow the better compatibility between the different software and hardware configuration.
Reliability: There should not be any failure in the network or if it occurs the recovery from a failure should be fast.
Security: A computer network should be secure so that the data transmitting over a network should be safe from unauthorised access. Also, the sent data should be received as it is at the receiving node, which means there should not be any loss of data during transmission.
Scalability: A computer network should be scalable which means it should always allow to add new computers (or nodes) to the already existing computer network. For example, a company runs 100 computers over a computer network for their 100 employees, lets say they hire another 100 employees and want to add new 100 computers to the already existing LAN then in that case the local area computer network should allow this
Basic components of a computer network
Server: Servers are computers that runs operating system and hold data that can be shared over a computer network.
Client: A client is a computer that is connected to other computers in the network and can receive data sent by other computers.
Transmission Media: All computers in a computer network are connected with each other through a transmission media such as wires, optical fibre cables, coaxial cables etc.
Network Interface card: Each system or computer in a computer network must have a card called network interface card (NIC). The main purpose of NIC is to format the data, send the data and receive the data at the receiving node.
Hub: Hub acts as a device that connects all the computer in a network to each other. Any request that comes from a client computer first received by Hub and then hub transmit this request over a network so that the correct server receives and respond to it.
Switch: Switch is similar to hub however instead of broadcasting a incoming data request it uses the physical device address in the incoming request to transfer the request to correct server computer.
Router: Router joins multiple computer networks to each other. For example lets say a company runs 100 computers over a local area network(LAN) and another company runs another LAN of 150 computers. These both LANs can be connected with each other through a internet connection which is provided by the router.
LAN cable: A wire that is used to connect more than one computers or other devices such as printers and scanner to each other.
Network
Topology:
The layout arrangement of the different devices
in a network
Star Topology
Bus Topology
Ring Topology
Tree Topology
Mesh Topology
Hybrid Topology
There are mainly three types
of computer networks based on their size:
1. Local Area Network (LAN)
2. Metropolitan Area Network (MAN)
3. Wide area network (WAN)
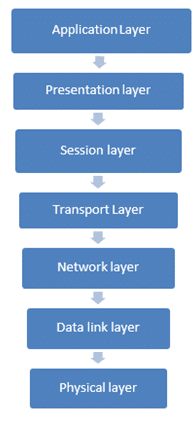
7 Layers Of The OSI Model
OSI Reference Model stands for Open system interconnection reference model which is used for communication in various networks.
The ISO (International organization for standardization) has developed this reference model for communication to be followed worldwide on a given set of a platform
Relationship Between Each Layer
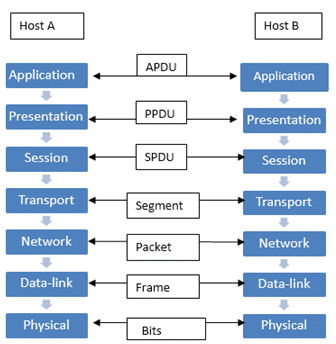
Enlisted below is the expansion of each Protocol unit exchanged between the layers:
- APDU– Application protocol data unit.
- PPDU– Presentation protocol data unit.
- SPDU– Session protocol data unit.
- TPDU– Transport protocol data unit (Segment).
- Packet– Network layer host-router protocol.
- Frame– Data-link layer host-router protocol.
- Bits– Physical layer host-router protocol.
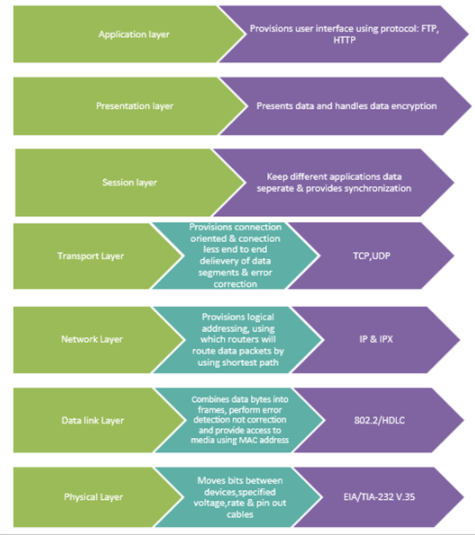
Roles & Protocols Used At Each Layer
Features Of The OSI Model
The various features of the OSI Model are enlisted below:
- Easy to understand the communication over wide networks through the OSI Reference Model architecture.
- Helps to know the details, so that we can get a better understanding of the software and hardware working together.
- Troubleshooting of faults is easier as the network is distributed in seven layers. Each layer has its own functionality, hence the diagnosis of the issue is easy and less time is taken.
- Understanding new technologies generation by generation becomes easier and adaptable with the help of the OSI Model.
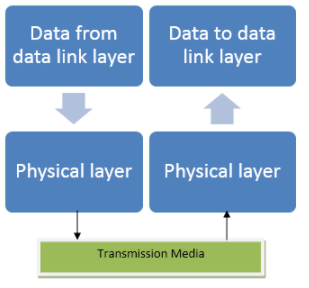
#1) Layer 1 – Physical layer
- The physical layer is the first and bottom-most layer of the OSI Reference Model. It mainly provides the bitstream transmission.
- It also characterizes the media type, connector type and signal type to be used for communication. Basically, the raw data in the form of bits i.e. 0’s & 1’s are converted into signals and exchanged over this layer. Data encapsulation is also done at this layer. The sender end and the receiving end should be in synchronization and the transmission rate in the form of bits per second is also decided at this layer.
- It provides a transmission interface between the devices and the transmission media and the type of topology to be used for networking along with the type of transmission mode required for transmission is also defined at this level.
- Usually, star, bus or ring topologies are used for networking and the modes used are half-duplex, full-duplex or simplex.
- Examples of layer 1 devices include hubs, repeaters & Ethernet cable connectors. These are the basic devices that are used at the physical layer to transmit data through a given physical medium which is suitable as per the network need.
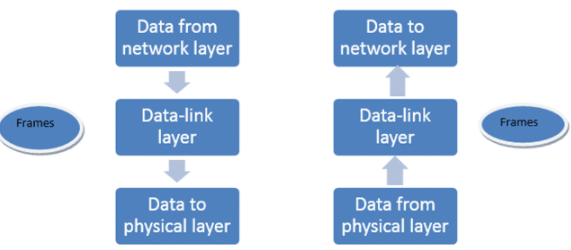
#2) Layer 2 – Data-link Layer
- Data-link layer is the second layer from the bottom of the OSI Reference Model. The main function of the data-link layer is to perform error detection and combine the data bits into frames. It combines the raw data into bytes and bytes to frames and transmits the data packet to the network layer of the desired destination host. At the destination end, the data-link layer receives the signal, decodes it into frames and delivers it to the hardware.
- MAC Address: Data-link layer supervises the physical addressing system called the MAC address for the networks and handles the access of the assorted network components to the physical medium.
- A media access control address is a unique device address and each device or component in a network has a MAC address on the basis of which we can uniquely identify a device of the network. It is a 12 digit unique address.
- Example of MAC address is 8C-95-19-9C-21-92 (having 6 octets, where the first 3 represent the OUI, the next three represent the NIC). It can also be known as the physical address. The structure of a MAC address is decided by the IEEE organization as it is globally accepted by all firms.
- Error Detection: Only error detection is done at this layer, not error correction. Error correction is done at the Transport layer.
- Sometimes data signals encounter some unwanted signals known as error bits. In order to conquer with the errors, this layer performs error detection. Cyclic Redundancy check (CRC) and checksum are few efficient methods of error checking. We will discuss these in the transport layer functions.
- Flow control & Multiple Access: Data which is sent in the form of a frame between the sender and a receiver over a transmission media at this layer, should transmit and receive at the same pace. When a frame is sent over a medium at a faster speed than the receiver’s working speed, then the data to be received at receiving node will be lost due to a mismatch in speed.
- In order to overcome these type of issues, the layer performs flow control mechanism.
There are two types of flow control process:
Stop and Wait for flow control: In this mechanism, it pushes the sender after the data is transmitted to stop and wait from the receiver’s end to get the acknowledgment of the frame received at the receiver end. The second data frame is sent over the medium, only after the first acknowledgment is received, and the process will go on.
Sliding window: In this process, both the sender and the receiver will decide the number of frames after which the acknowledgment should be exchanged. This process is time-saving as fewer resources are used in the flow control process.
- This layer also provisions to provide access to multiple devices to transmit through the same media without collision by using CSMA/CD (carrier sense multiple access/collision detection) protocols.
- Synchronization: Both the devices between which data sharing is taking place should be in synchronization with each other at both the ends so that data transfer can take place smoothly.
- Layer-2 Switches: Layer-2 switches are the devices which forward the data to the next layer on the basis of the physical address (MAC address) of the machine. Firstly it gathers the MAC address of the device on the port on which the frame is to be received and later learns the destination of the MAC address from the address table and forwards the frame to the destination of the next layer. If the destination host address is not specified then it simply broadcasts the data frame to all the ports except the one from which it learned the address of the source.
- Bridges: Bridges is the two port device which works on the data link layer and is used to connect two LAN networks. In addition to this, it behaves like a repeater with an additional function of filtering the unwanted data by learning the MAC address and forwards it further to the destination node. It is used for the connectivity of networks working on the same protocol.
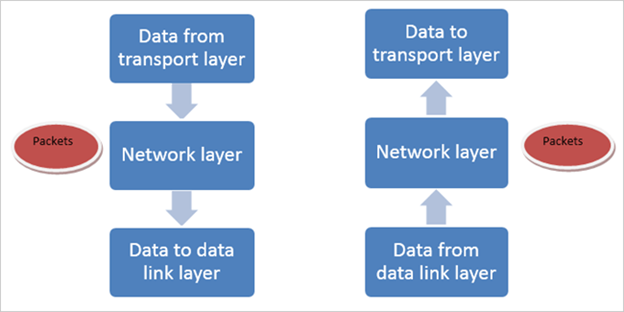
#3) Layer 3 – Network Layer
The network layer is the third layer from the bottom. This layer has the accountability to accomplish the routing of data packets from the source to destination host between the inter and intra networks operating on the same or different protocols.
Apart from the technicalities, if we try to understand what it really does?
The answer is very simple that it finds out the easy, shortest, and time-efficient way out between the sender and the receiver to exchange data using routing protocols, switching, error detection and addressing techniques.
- It performs the above task by using a logical network addressing and subnetting designs of the network. Irrespective of the two different networks working on the same or different protocol or different topologies the function of this layer is to route the packets from the source to destination by using the logical IP addressing and routers for communication.
- IP Addressing: The IP address is a logical network address and is a 32-bit number which is globally unique for each network host. It principally consists of two parts i.e. network address & host address. It is generally denoted in a dotted-decimal format with four numbers split by dots. For Example, the dotted-decimal representation of the IP address is 192.168.1.1 which in binary will be 11000000.10101000.00000001.00000001, and is very hard to remember. Thus usually the first one is used. These eight bits sector are known as octets.
- Routers work at this layer and are used for communication for inter and intra network-wide area networks (WAN’s). Routers who transmit the data packets between the networks do not know the exact destination address of the destination host for which the packet is routed, rather they only know the location of the network to which they belong to and use the information that is stored in the routing table to establish the path along which the packet is to be delivered to the destination. After the packet is delivered to the destination network, it then is delivered to the desired host of that particular network.
- For the above series of procedure to be done the IP address has
two parts. The first part of IP address is network address and the last part is
the host address.
- Example: For the IP address 192.168.1.1. The network address will be 192.168.1.0 and the host address will be 0.0.0.1.
Subnet Mask: The network address and the host address defined in the IP address is not solely efficient to determine that the destination host is of the same sub-network or remote network. The subnet mask is a 32-bit logical address that is used along with the IP address by the routers to determine the location of the destination host to route the packet data.
Example for combined usage of IP address & subnet mask is shown below:
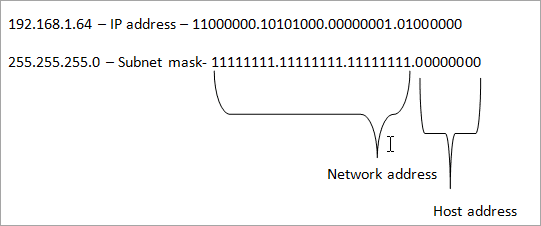
For the above Example, by using a subnet mask 255.255.255.0, we get to know that the network ID is 192.168.1.0 and the host address is 0.0.0.64. When a packet arrives from 192.168.1.0 subnet and has a destination address as 192.168.1.64, then the PC will receive it from the network and process it further to the next level.
Thus by using subnetting, the layer-3 will provide an inter-networking between the two different subnets as well.
The IP addressing is a connectionless service, thus the layer -3 provides a connectionless service. The data packets are sent over the medium without waiting for the recipient to send the acknowledgment. If the data packets which are big in size are received from the lower level to transmit, then it splits it into small packets and forwards it.
At the receiving end, it again reassembles them to the original size, thus becoming space efficient as a medium less load.
#4) Layer 4 – Transport Layer
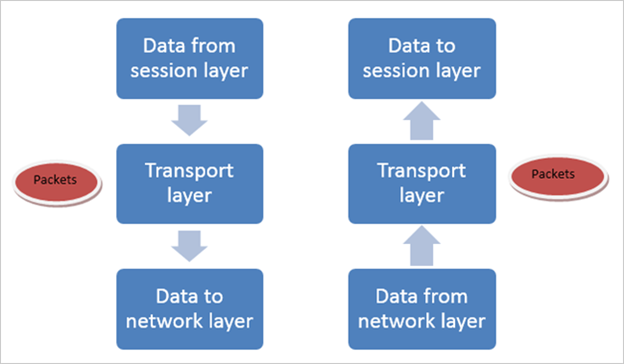
The fourth layer from the bottom is called the transport layer of the OSI Reference model.
(i) This layer guarantees an end to end error-free connection between the two different hosts or devices of networks. This is the first one which takes the data from the upper layer i.e. the application layer, and then splits it into smaller packets called the segments and dispenses it to the network layer for further delivery to the destination host.
It ensures that the data received at host end will be in the same order in which it was transmitted. It provides an end to end supply of the data segments of both inter and intra sub-networks. For an end to end communication over the networks, all devices are equipped with a Transport service access point (TSAP) and are also branded as port numbers.
A host will recognize its peer host at the remote network by its port number.
(ii) The two transport layer protocols include:
- Transmission control protocol (TCP)
- User Datagram Protocol (UDP)
TCP is a connection-oriented and reliable protocol. In this protocol, firstly the connection is established between the two hosts of the remote end, only then the data is sent over the network for communication. The receiver always sends an acknowledgment of the data received or not received by the sender once the first data packet is transmitted.
After receiving the acknowledgment from the receiver, the second data packet is sent over the medium. It also checks the order in which the data is to be received otherwise data is re-transmitted. This layer provides an error correction mechanism and flow control. It also supports client/server model for communication.
UDP is a connectionless and unreliable protocol. Once data is transmitted between two hosts, the receiver host doesn’t send any acknowledgment of receiving the data packets. Thus the sender will keep on sending data without waiting for an acknowledgment.
This makes it very easy to process any network requirement as no time is wasted in waiting for acknowledgment. The end host will be any machine like a computer, phone or tablet.
This type of protocol is widely used in video streaming, online games, video calls, voice over IP where when some data packets of video are lost then it doesn’t have much significance, and can be ignored as it doesn’t make much impact on the information it carries and doesn’t have much relevance.
(iii) Error Detection & Control: Error checking is provided in this layer because of the following two reasons:
Even if no errors are introduced when a segment is moving over a link, it can be possible for errors to be introduced when a segment is stored in the router’s memory (for queuing). The data link layer is not able to detect an error in this scenario.
There is no assurance that all the links between the source and destination will provide error scrutiny. One of the links may be using a link layer protocol which doesn’t offer the desired outcomes.
The methods used for error check and control are CRC (cyclic redundancy check) and checksum.
CRC: The concept of CRC (Cyclic Redundancy Check) grounds on the binary division of the data component, as the remainder of which (CRC) is appended to the data component and sent to the receiver. The recipient divides data component by an identical divisor.
If the remainder comes up to zero then the data component is allowed to pass to forward the protocol, else, it is assumed that the data unit has been distorted in transmission and the packet is discarded.
Checksum Generator & checker: In this method, the sender uses the checksum generator mechanism in which initially the data component is split into equal segments of n bits. Then, all the segments are added together by employing 1’s complement.
Later, it complements once again, and now it turns into checksum and then is sent along with the data component.
Example: If 16 bits is to be sent to the receiver and bits are 10000010 00101011, then the checksum that will be transmitted to the receiver will be 10000010 00101011 01010000.
Upon receiving the data unit, the receiver divides it into n equal size segments. All the segments are added using 1’s complement. The result is complemented once more and If the result is zero, the data is accepted, else discarded.
This error detection & control method permits a receiver to rebuild the original data whenever it is found corrupted in transit.
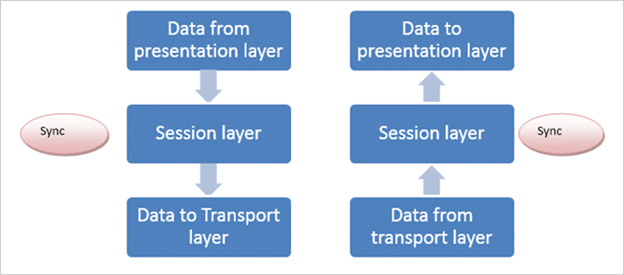
#5) Layer 5 – Session Layer
This layer permits the users of different platforms to set up an active communication session between themselves.
The main function of this layer is to provide sync in the dialogue between the two distinctive applications. The synchronization is necessary for efficient delivery of data without any loss at the receiver end.
Let’s understand this with the help of an Example.
Assume that a sender is sending a big data file of more than 2000 pages. This layer will add some checkpoints while sending the big data file. After sending a small sequence of 40 pages, it ensures the sequence & successful acknowledgment of data.
If verification is OK, it will keep repeating it further till the end otherwise it will re-synchronize and re-transmit.
This will help in keeping the data safe and the whole data host will never completely get lost if some crash happens. Also, token management, will not allow two networks of heavy data and of the same type to transmit at the same time.
#6) Layer 6 – Presentation Layer
As suggested by the name itself, the presentation layer will present the data to its end users in the form in which it can easily be understood. Hence, this layer takes care of the syntax, as the mode of communication used by the sender and receiver may be different.
It plays the role of a translator so that the two systems come on the same platform for communication and will easily understand each other.
The data which is in the form of characters and numbers are split into bits before transmission by the layer. It translates the data for networks in the form in which they require it and for devices like phones, PC, etc in the format they require it.
The layer also performs data encryption at the sender’s end and data decryption at the receiver’s end.
It also performs data compression for multimedia data before transmitting, as the length of multimedia data is very big and much bandwidth will be required to transmit it over media, this data is compressed into small packets and at the receiver’s end, it will be decompressed to get the original length of data in its own format.
#7) Top Layer – Application Layer
This is the topmost and seventh layer of the OSI reference model. This layer will communicate with the end users & user applications.
This layer grants a direct interface and access to the users with the network. The users can directly access the network at this layer. Few Examples of services provided by this layer include e-mail, sharing data files, FTP GUI based software like Netnumen, Filezilla (used for file sharing), telnet network devices etc.
There is vagueness in this layer as is not all user-based information and the software can be planted into this layer.
For Example, any designing software can’t be put directly at this layer while on the other hand when we access any application through a web browser, it can be planted at this layer as a web browser is using HTTP (hypertext transfer protocol) which is an application layer protocol.
Therefore irrespective of the software used, it is the protocol used by the software that is considered at this layer.
Software testing programs will work on this layer as the application layer provides an interface to its end users to test the services and their uses. The HTTP protocol is mostly used for testing at this layer but FTP, DNS, TELNET can also be used as per the requirement of the system and network in which they are operating.
LAN Vs WAN Vs MAN: Exact Difference Between Types Of Network
Local Area Network (LAN)
Local area networks are constructed for small geographical areas within the range of 1-5 km such as offices, schools, colleges, small industries or a cluster of buildings. It is extensively used to design and troubleshoot.
Let’s understand it with the help of an Example:
PC’s, laptops and workstations in an office are generally inter-connected with each other by using LAN networks through which we can share data files, software, e-mail and access hardware such as printers, FAX etc. All the resources or host are connected via a single cable in LAN.
The transmission rate of LAN ranges from 4Mbps to 16Mbps and can maximize up to 100 Mbps (Mbps stands for megabits per second). We can use any type of network topology which meets the need of the network such as a ring or bus for the interconnection of the host in LAN networks.
Ethernet, token ring, Fiber distributed data interchange (FDDI), TCP/IP and asynchronous transfer mode (ATM) are the most common protocol that is used in this network.
LAN networks are of various kinds depending upon the type of media, topology, and protocols they are using for communication.
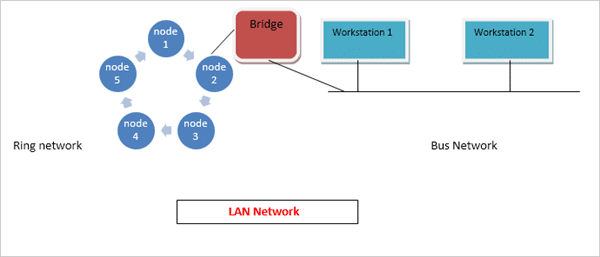
Applications of LAN
(i) The first application of the LAN network is that it can be easily implemented as a server-client model network. For Example, In a university, suppose all the hosts are connected through LAN, then one of the PC can be converted into Server and all the other PC’s will be clients which can have access to the data stored on the client computers.
By having this kind of a facility the Dean and the professors of the university can easily share data or resources with each other as they are on the same network.
(ii) As all the workstations are connected locally, if they want to pass on some internal communication, then each node can communicate with one another without having any internet connection.
(iii) The resources like printers, hard-disk, and FAX machine can publicly use all the nodes in LAN networks.
(iv) Software testers can also use LAN network for sharing their testing tools within an office or within a factory using the client-server model of the networking system. The software can be put on one centralized server whose data is made accessible by all the client PCs with the help of a local administrator.
The clients can also suggest the changes if they require any of their business purposes on the same network regarding the tool. Thus sharing a software tool locally will make the work easy and speed up the ongoing process.
Advantages of LAN
Given below are the various advantages of LAN:
- In an office which is connected via LAN network, we can share the hardware and software resources like printers, FAX, drivers and hard-disk as they are on one platform and thus this type of network turns out to be cost-effective.
- As being connected on the network, the offices or firms using the same type of software for job purposes need not purchase separately for each of the host clients as the software can easily be shared with everyone on an equal level.
- LAN network works as a client-server model, therefore data can be stored centrally on one PC called as a server in a network and it can be accessible to all the other client PC’s via LAN. By following this method, we need not store data locally at one single node.
- Communication will be handy and economical by using LAN network.
- Internet cafe owners use the LAN network to provide internet connections to multiple nodes and users connected via a single internet connection. This makes the use of the internet a cost-effective one.
Disadvantages of LAN
The disadvantages of LAN are:
- LAN networks come out to be cost-effective and time-saving, as we can share various resources on one platform. However, the initial installation cost of the network is very high.
- It is having a geographical area limitation and can only cover a small area (1-5 km).
- As it works on a single cable, if it gets faulty then the overall network will stop working. Hence, it needs a full -time maintenance officer called an administrator.
- Crucial Data of offices or factories is saved on a single server which can easily be accessible by all the nodes thus it is having all time data security issues as any unauthorized person can also access the confidential data.
Metropolitan Area Network (MAN)
MAN covers a bigger geographical area than LAN Network E.g. cities and districts. It can also be considered as a superior version of the LAN network. As LAN covers only a minor area of the network, MAN is designed to connect a city or two villages together through it.
The area covered by MAN is generally 50-60 km. Fiber optical cable and twisted pair cables are used for connectivity for communication through MAN networks.
MAN can also be considered as a group of one or more LAN networks connected together through a single cable. RS-232, X-25, Frame Relay, and ATM are the common protocol practice for communication in MAN.
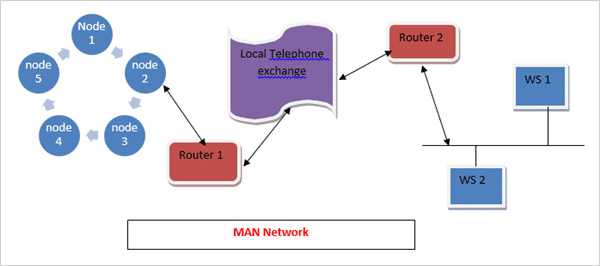
Application of MAN
#1) Various government bodies use MAN network for inter-connectivity between their department’s offices situated at different locations.
For Example, MAN can be used to connect various police stations which are situated within a district or city with each other. The officers can easily communicate with each other and quickly pass on the important data and an urgent message over this network without any need for the Internet connection.
#2) Any private firm can also use a MAN network for inter-connectivity between their offices situated at two different towns of a district. The firm can share resources like data file, images, software & hardware parts etc., with each other. Thus it provides resource sharing over a large distance than the LAN networks.
Advantages of MAN
Given below are the various advantages of MAN:
- It is very efficient and swift for communication over fiber optic cable for interconnection of networks in cities.
- It serves many villages and cities and thus provides great inter-connectivity at a low cost.
- It works on ring or bus topology with a protection link, thus data can be transmitted or received simultaneously over nodes and if one link fails the other will keep the network live.
Disadvantages of MAN
The disadvantages of MAN are:
- Depending upon the distance between two nodes, the cable length required for inter-connection differs every time. Thus greater will be the cable length, the more will be the cost of the network.
- Security is a big concern for this network as for such a big distance anyone can hack the network. We can’t put security at each level of the network, hence it becomes easier for unwanted people to access it for their own benefits.
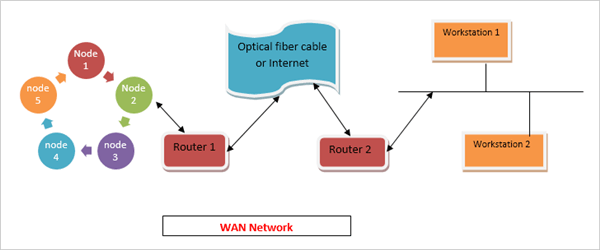
Wide Area Network (WAN)
WAN is widely used in long-distance communication systems.
It covers bigger areas i.e right from a state to a country. Therefore the geographical area it covers is from 100 to several 1000 km. WAN networks are complex in nature, however, they are widely used in mobile communications as they cover up long distances.
Generally, fiber optic cable is used as a media for transmission in this system.WAN works on physical, data-link and network layers of the OSI Reference model.
Routers are used in WAN network for communication as they provide the shortest path for communication over long distance using routing tables. Routers also provide a secure and fast rate of transmission.
Different types of data need to be transmitted over the network like image, voice, video and data files. Therefore the routers use packet switching technique for sending and receiving data between nodes. It is not necessary that the device used should be a router only, other devices such as switches, bridges etc., are also used for connectivity.
Routers have routing tables by which they learn the host and destination address for delivery of the data packet and that in turn is the shortest path for transmission. By following this mechanism a source end router will communicate with the far end destination router and exchange the data packets.
Routers and switches have internal memories. Thus when a data packet has arrived at a switch node for delivery, it uses to store and forward the technique for data transmission.
If a media is busy then the node (switch or router) stores the data packets and queues it and when it finds the link free, it then transmits it further. Therefore, packet switching uses data store, queuing and forward technique in the case when the link is found busy.
If the link is free then it just stores and forwards the packet and no queuing is required. For fast and error-free transmission, high bandwidth STM links are used to connect two distinct end nodes.
STM links provide fully synchronous transmission between the sender and a receiver and also provide error detection. In case any error is found then the packet is discarded and is re-transmitted. Routers are most popularly used by Mobile networking companies as they provide fast and reliable communication.
The WAN network can be of two types:
- Wired WAN – This uses OFC as the media for communication
- Wireless WAN – Satellite communication is a type of WAN network.
Applications of WAN
#1) Consider the case of an MNC where the head office is situated in Delhi and the regional offices are situated in Bangalore and Mumbai. Here, all are connected through a WAN network.
If HOD’s of corporate office want to share some data with their regional office mates then they can share data (image, video or any data of big size) by saving it on the centralized node which can be accessible by everyone in the organization and is on one single network only.
The centralized server is maintained by an administrator who has the rights to grant access to the users connected to the main server. The administrator will allow sharing only that information which is of the scope of the client nodes.
The rights are reserved for confidential data and only a few higher level authorities of the company will have the rights to access it.
The software testers can also work in this scenario and can share their tools with their colleagues situated hundreds of km away in just a few minutes by using WAN network.
#2) The WAN networks are used for military services. The satellite mode of transmission is used in this setup. Military operations require highly secured network for communication. Thus WAN is used in this scenario.
#3) Railways reservation and Airlines use WAN networks. The client nodes are situated all over the country and are connected to a centralized server node and all are connected to one network. Thus booking can be done from anywhere in the country.
#4) Mobile operators and service providers like NSN or Ericsson use WAN network to provide mobile services in a particular circle. Different circles of a country are also connected with each other through WAN networks. The connections are made through routers and switches using higher bandwidth STM links.
#5) The WAN network also works in master-slave scenario and main & protection link topology.
If one link fails then the data transmission will keep moving smoothly by a protection link. By master-slave scenario, if the master device fails then the slave will act as a master and will take all the responsibilities for data packet transmission without any delay and failure.
Advantages of WAN
Given below are the various advantages of WAN:
- It connects various cities and states with one another. Hence, large scale industries can be connected to one single network.
- N number of nodes can be connected over this network for sharing software.
- As routers are used for sending and receiving the end of the network, the rate of transmission is very high even if we send large sized files of more than 10 MB.
- All users connected via WAN will remain in synchronization with each other at all the time, therefore, there will be no chances of communication gap between them.
- The users can share the hardware like printers, hard-disk etc. with each other and there is no need to buy a separate connection for internet as all type of communication can be done within as they are being on one network only.
Disadvantages of WAN
The disadvantages of WAN are:
- Confidential and important data is shared over a long distance, hence there are chances for unwanted people to try to interrupt and hack the data. Therefore there is always a need to purchase a security firewall for the network to protect it from the outside threats.
- Set-up of WAN network is complex and costly.
- As WAN network is spread over a very large distance, we need to deploy a local administrator at every intermediate point to ensure its maintenance and fault control.
- Local monitoring of such wide networks is not sufficient enough to maintain it properly. Therefore, some companies, like mobile operators will set up a NOC and purchase a GUI based centralized monitoring tool for operation and maintenance purpose. This will cost them a lot of manpower and money for running it smoothly.
Conclusion
In this tutorial, we have studied the features, applications, advantages, and disadvantages of LAN, MAN, and WAN computer networking system. All three types of networking systems have their own significance in different fields.
MAN networks are very rare in use as they have lots of security issues and the installation costs are very high as well.
According to the latest trend of technology, LAN networks are most widely used for local level communications within offices and colleges while WAN is widely used in mobile and LTE long distance communications where the connectivity is based on the fiber cable.
LAN networks are very cost effective as once setup is done there is no need of further expenditure while in WAN networks, by the increase in the number of nodes in a network the overall cost of the network increases. Therefore WAN networks are very costly and require high maintenance too.
The speed of LAN is more than the speed of WAN networks. Depending upon the business requirement and budget of the network, we need to decide the type of network which would be suitable for effective implementation.
Subnet Mask (Subnetting) & IP Subnet Calculator
IP addressing is used to recognize the host of a network and uniquely identify a particular device of the Network.
Whereas subnetting is used in combination with IP addressing to develop several logical addressing that exists within a single network.
We will see the different classes of a Network along with their roles and significance in computer networking. In our daily life, we human beings identify each other with our names, similarly, the routers and switches recognize their neighboring device and network with an IP address and a subnet mask.
Understanding IP Addressing
The overall phenomenon of logical addressing works on the Layer-3 of the OSI reference model and the network components like routers and switches are the host devices that are most popularly used.
An IP Address is a 32-bit logical address that distinctively classifies a host of the network. The host can be a computer, Mobile handset or even a tablet. The 32 bits binary IP address is made up of two distinctive parts i.e. The Network address and the Host address.
It also has 4 octets as each octet is having 8 bits. This octet is converted into decimal and is separated by a format i.e. dot. Thus it is represented in a dotted-decimal format. The range of an octet in binary is from 00000000 to 11111111 and in decimal from 0 to 255.
Example of an IP Address format:
192.168.1.64 (in decimal)
11000000.10101000.00000001.01000000 (in binary).
The binary one is difficult to memorize thus, in general, the dotted decimal format is used worldwide for representation of the logical addressing.
Let’s understand in detail how the binary octet values are converted into decimal values:
There are 8 bits and each bit has the value of 2 to the power n (2^n). The rightmost have the value 2^0 and left most have the value 2^7.
So the value of each bit is as follows:
2^7 2^6 2^5 2^4 2^3 2^2 2^1 2^0 (^ denotes the power)
Thus the result would be:
128+ 64+ 32+ 16+ 8+ 4+ 2+ 1
When all the bits are 1 then the values come out to be 255 (128+64+32+16+8+4+2+1= 255).
Suppose all the bits of an octet is not 1. Then see how we can calculate the IP address:
1 0 0 1 0 0 0 1, 128+0+0+16+0+0+0+1= 145.
By combining the bits of the octets in different combinations according to the need, we can derive the overall IP address of the desired network. As per the requirement, these are divided into various classes of a network called as class A, class B, class C, class D, and class E.
Most popularly class A, B and C are used for commercial purposes and class D and E have reserved rights.
Network Classes And Subnet Mask
The organization which governs the internet has divided the IP addresses into different classes of the network.
Each class is identified by its subnet mask. By the categorization of a default subnet mask, we can easily identify the class of an IP address of the network. The first octet of an IP address identifies the particular class of an IP address.
The classification is shown with the help of the below table and figure.
| Class | Ist octet Decimal Range | Network/Host ID | Default subnet mask |
| A | 1 to 126 | N.H.H.H | 255.0.0.0 |
| B | 128 to 191 | N.N.H.H | 255.255.0.0 |
| C | 192 to 223 | N.N.N.H | 255.255.255.0 |
| D | 224 to 239 | Reserved for Multicasting | |
| E | 240 to 254 | Experimental |
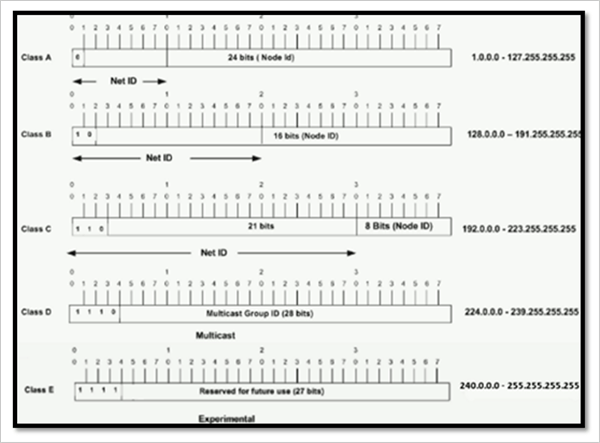
- The class ‘A’ Address ranging from 127.0.0.0 to 127.255.255.255 cannot be used and is reserved for loopback and diagnostic functions. The numbers of hosts which can be connected to this network are greater than 65536 hosts.
- The number of hosts connected within the class B networks is from 256 to 65534 hosts.
- The number of hosts connected within the class C network is less than 254 hosts. Therefore the class C network mask is perfect for the minor networks which are known as subnetworks. We utilize the bits from the last octet of class C for constructing mask. Thus we need to rearrange and optimize the subnet depending upon the availability of the bits.
Below table will show the masks that can be drawn on with Class C networks.
| Subnet Mask | Last octet binary Value | No. of hosts connected |
| 255.255.255.128 | 10000000 | 126 |
| 255.255.255.192 | 11000000 | 62 |
| 255.255.255.224 | 11100000 | 30 |
| 255.255.255.240 | 11110000 | 14 |
| 255.255.255.248 | 11111000 | 6 |
| 255.255.255.252 | 11111100 | 2 |
We have studied about the network class and subnet mask phenomenon of computer networking. Now let’s see how the mask will help us to classify the network ID and host ID part of an IP address.
Let us assume the case of a class A IP address:
For Example, take a pair of IP address and subnet mask 10.20.12.2 255.0.0.0
#1) Convert this Combination into a binary value:
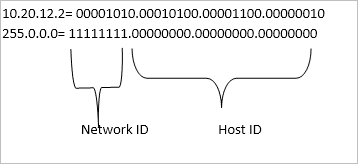
#2) The bits corresponding to the subnet mask with all 1’s represent the network ID as it is a class A network and the first octet represents the network ID. The bits corresponding to all 0’s of the subnet mask is the host ID. Thus the network ID is 10 and the host ID is 20.12.2
#3) From the given subnet, we can also calculate the IP range of a particular network. If the IP is 10.68.37.128 (assuming class A case)
Subnet mask: 255.255.255.224
IP range =256-224= 32.
Out of 32 IP’s, ideally one is used for the gateway, second is for the network
IP and the third is for broadcast IP.
Thus total usable IP’s are 32-3= 29 IP’s.
The IP range will be 10.68.27.129 to 10.68.27.158.
Subnetting
Subnetting allows us to create various sub-networks or logical networks within one network of a particular class of the network. Without subnetting, it is almost unrealistic to create big networks.
For constructing a big networking system, every link must have a unique IP address with every device on that linked network which is being the participant of that network.
With the help of a subnetting technique, we can split the large networks of a particular class (A, B or C) into smaller subnetworks for inter-connection between each node which are situated at different locations.
Each node on the network would have a distinctive IP and subnet mask IP. Any switch, router or gateway that connects n networks has n unique Network ID and one subnet mask for each of the network it interconnects with.
The formulae of subnetting is as follows:
2^n >= requirement.
The formulae of a number of hosts per subnet is as follows:
2^n -2
Now let’s understand the overall process with the help of an Example:
We have taken an example of Class C network ID with a default subnet mask.
Suppose Network ID/IP address is: 192.168.1.0
Default Subnet mask: 255.255.255.0 (in decimal)
Default Subnet mask: 11111111.11111111.11111111.00000000 (in binary)
Thus the number of bits are 8+8+8+0= 24 bits. As mentioned earlier, for subnetting in class C network, we will borrow bits from the host portion of the subnet mask.
Therefore, to customize the subnet as per requirement:
We take a subnet mask of 255.255.255.248 (in decimal)
11111111.11111111.11111111.11111000 (in binary).
From the above binary notation, we can see that the last 3 bits of the last octet can be used for host ID addressing purpose.
Thus the number of subnets= 2^n = 2^3= 8 subnets (n=3).
Number of hosts per subnet= 2^n -2= 2^3 -2= 8-2= 6 Subnets i.e. usable Host IP.
Now the IP addressing scheme is as follows:
| Network IP | First Usable IP | Last Usable IP | Broadcast IP |
| 192.168.1.0 | 192.168.1.1 | 192.168.1.6 | 192.168.1.7 |
| 192.168.1.8 | 192.168.1.9 | 192.168.1.14 | 192.168.1.15 |
| 192.168.1.16 | 192.168.1.17 | 192.168.1.22 | 192.168.1.23 |
| 192.168.1.24 | 192.168.1.25 | 192.168.1.30 | 192.168.1.31 |
| 192.168.1.32 | 192.168.1.33 | 192.168.1.38 | 192.168.1.39 |
| 192.168.1.40 | 192.168.1.41 | 192.168.1.46 | 192.168.1.47 |
| 192.168.1.48 | 192.168.1.49 | 192.168.1.54 | 192.168.1.55 |
| 192.168.1.56 | 192.168.1.57 | 192.168.1.62 | 192.168.1.63 |
The subnet mask for all the above IP’s in the table is common i.e. 255.255.255.248.
With the help of the above example, we can clearly see, how subnetting helps us to construct inter-networking between various links and nodes of the same subnetwork. All these above IP’s can be used for inter-networking the devices within the overall network.
Note: Subnet mask is most widely used everywhere in a computer networking system. Hence, there is one more method to represent the subnet mask of a particular network which is chosen and standardized as it is easy to denote and memorize.
Subnet mask– 255.255.255.248 (binary)
11111111.11111111.11111111.11111000 (decimal notation)
From the decimal notation we can calculate the number of bits having 1 in each octet:
8+8+8+5= 29
Thus the Subnet mask can be denoted as /29.
With Network ID it can be denoted as 192.168.1.9/29.
From the above notation, anyone who knows the standard notation and formulae of subnetting can understand that the IP is using a subnet mask of 255.255.255.248 or /29.
The different Subnetting scheme in binary and decimal notation is shown below:
| Subnet Mask | Notation in decimal | Notation in Binary | Number of Usable IP |
| /24 | 255.255.255.0 | 11111111.11111111.11111111.00000000 | 254 |
| /25 | 255.255.255.128 | 11111111.11111111.11111111.10000000 | 126 |
| /26 | 255.255.255.192 | 11111111.11111111.11111111.11000000 | 62 |
| /27 | 255.255.255.224 | 11111111.11111111.11111111.11100000 | 30 |
| /28 | 255.255.255.240 | 11111111.11111111.11111111.11110000 | 14 |
| /29 | 255.255.255.248 | 11111111.11111111.11111111.11111000 | 6 |
| /30 | 255.255.255.252 | 11111111.11111111.11111111.11111100 | 2 |
The ‘/’ notation method of the subnet mask is most widely used as it is easy to memorize and the binary notation and decimal are very lengthy in size.
As we are denoting the mask scheme while interconnecting the network components through the figure, if we use the decimal and binary method then the overall diagram will become very complex and difficult to understand.
There are so many IP’s on the platform to be shown and it becomes difficult to memorize as well. Thus generally, people who are familiar with routing and IP addressing scheme use short notation methods in figures and diagrams.
Example 1:
Understanding Subnetting with an Example of Interconnection of Network Devices:
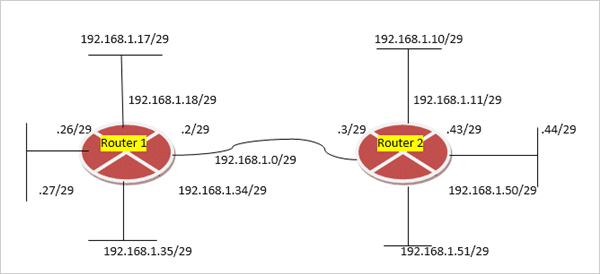
The above figure shows how subnetting is used for interconnection of subnetworks. Firstly, as per our need for the number of hosts required to be connected and meet the other requirements of the network, we customize the subnet mask and network ID accordingly and assign to the devices thereafter.
The above network is using class C network mask and /29 subnet mask means network IP can be divided into 8 subnets. Each router has a unique IP address for each linked subnetwork.
There is an important point to be noticed that the more the bits we carry from the subnet mask for host ID then the more will be the subnets obtainable for the network.
Example 2:
Class B Network:
| Subnet mask | Notation in binary | Number of Usable IP | Number of Subnets |
| 255.255.128.0 | 11111111.11111111.10000000.00000000 | 32766 | 2 |
| 255.255.192.0 | 11111111.11111111.11000000.00000000 | 16382 | 4 |
| 255.255.224.0 | 11111111.11111111.11100000.00000000 | 8190 | 8 |
| 255.255.240.0 | 11111111.11111111.11110000.00000000 | 4094 | 16 |
| 255.255.248.0 | 11111111.11111111.11111000.00000000 | 2046 | 32 |
| 255.255.252.0 | 11111111.11111111.11111100.00000000 | 1022 | 64 |
| 255.255.254.0 | 11111111.11111111.11111110.00000000 | 510 | 128 |
| 255.255.255.0 | 11111111.11111111.11111111.00000000 | 254 | 256 |
| 255.255.255.128 | 11111111.11111111.11111111.10000000 | 126 | 512 |
| 255.255.255.192 | 11111111.11111111.11111111.11000000 | 62 | 1024 |
| 255.255.255.224 | 11111111.11111111.11111111.11100000 | 30 | 2048 |
| 255.255.255.240 | 11111111.11111111.11111111.11110000 | 14 | 4096 |
| 255.255.255.248 | 11111111.11111111.11111111.11111000 | 6 | 8192 |
| 255.255.255.252 | 11111111.11111111.11111111.11111100 | 2 | 16384 |
The above table shows the details of the number of subnets and hosts that can be connected per subnet mask by using Class B subnetting Scheme.
For connecting a host in big quantity and WAN communication systems, the Class B subnetting is very effective as it gives a wide range of IP’s for configuration.
What Is IP Subnet Calculator?
As mentioned in detail above the concept of IP addressing and subnetting, the subnets and supernet networks are derived from a big network to create small networks for interconnection of various network devices, situated far apart with each other and assigning the unique IP address and subnet mask to them for communication with each other.
The IP calculator will give output for the value of broadcast IP address, usable IP range of the host devices, subnet mask, IP class and the total number of hosts by entering the subnet mask and the IP address of the particular network as the input value.
The IP calculator gives the result for both IPV4 and IPV6 network protocol classes of networks.
Why Is IP Calculator Needed?
There are different classes of networks that are used for networking systems and out of those for commercial purposes the class A, B and C are most widely used.
Now let us understand the need for an IP calculator with the help of an example. If we need to calculate the host range, broadcast IP, etc.
Example #1: For a class C network with the network IP 190.164.24.0 and subnet mask 255,255.255.240 means /28 in CIDR notation.
Then we can manually calculate it as by the mathematical formulae which we have explained earlier in this tutorial.
We will borrow the host IP from the last octet for the subnetting which is 11111111.11111111.11111111.11110000
Here the no. of subnets are 2^n
= 2^4 = 16 subnets (n=4).
Number of host per subnet is
2^n -2 = 2^4 -2 = 14 subnets means 14 usable host IP.
For the network IP 190.164.24.0,
| Network IP | First Usable IP | Last Usable IP | Broadcast IP |
| 190.164.24.0 | 190.164.24.1 | 190.164.24.14 | 190.164.24.15 |
| 190.164.24.16 | 190.164.24.17 | 190.164.24.30 | 192.164.24.31 |
| 190.164.24.32 | 190.164.24.33 | 190.164.24.46 | 192.164.24.47 |
| 190.164.24.48 | 190.164.24.49 | 190.164.24.62 | 192.164.24.63 |
| 190.164.24.64 | 190.164.24.65 | 190.164.24.78 | 192.164.24.79 |
| 190.164.24.80 | 190.164.24.81 | 190.164.24.94 | 192.164.24.95 |
| 190.164.24.96 | 190.164.24.97 | 190.164.24.110 | 192.164.24.111 |
| 190.164.24.112 | 190.164.24.113 | 190.164.24.126 | 192.164.24.127 |
| 190.164.24.128 | 190.164.24.129 | 190.164.24.142 | 192.164.24.143 |
| 190.164.24.144 | 190.164.24.145 | 190.164.24.158 | 192.164.24.159 |
| 190.164.24.160 | 190.164.24.161 | 190.164.24.174 | 192.164.24.175 |
| 190.164.24.176 | 190.164.24.177 | 190.164.24.190 | 192.164.24.191 |
| 190.164.24.192 | 190.164.24.193 | 190.164.24.206 | 192.164.24.207 |
| 190.164.24.208 | 190.164.24.209 | 190.164.24.222 | 192.164.24.223 |
| 190.164.24.224 | 190.164.24.225 | 190.164.24.238 | 192.164.24.239 |
| 190.164.24.240 | 190.164.24.241 | 190.164.24.254 | 192.164.24.255 |
The subnet mask is common for all these IP ranges which are 255.255.255.240.
The whole procedure of calculating this manually is lengthy.
Example # 2: Calculating the same parameters for subnetting for the class A network IP.
The IP address is 10.0.0.0
The subnet mask is 255.252.0.0.
(/14 in CIDR notation)
Now the number of usable hosts
per subnet is 262,142.
Thus for calculating the network parameters in such a kind of huge networks, the subnet calculator is designed. It is basically a software tool and calculates the desired value automatically by just entering some basic parameters like network IP and subnet mask.
The output is more precise, accurate and for the user who is constructing the subnets and supernets from the one big network and is also time-saving.
Also, it is very easy and simple to use and is mostly used in the case of class A and class B networks as here the no. of usable IP and host range is in from thousands to millions.
The network address is 10.0.0.0
The subnet mask is 255.252.0.0
(/14) in CIDR notation.
The number of hosts will be
262144 and the number of subnets will be 64.
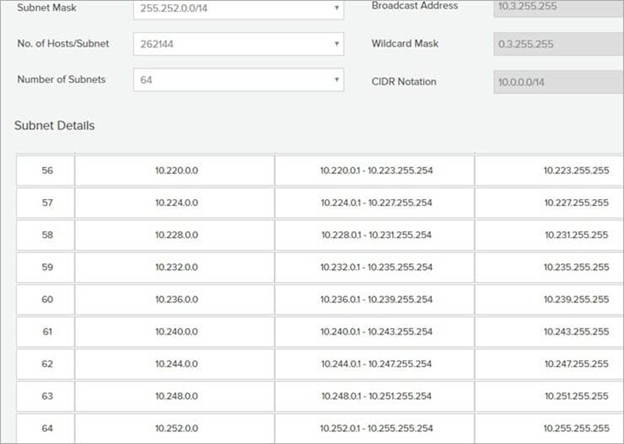
Now see how we can get this from the tool with the help of the below set of screenshots in three parts as the result is very large.
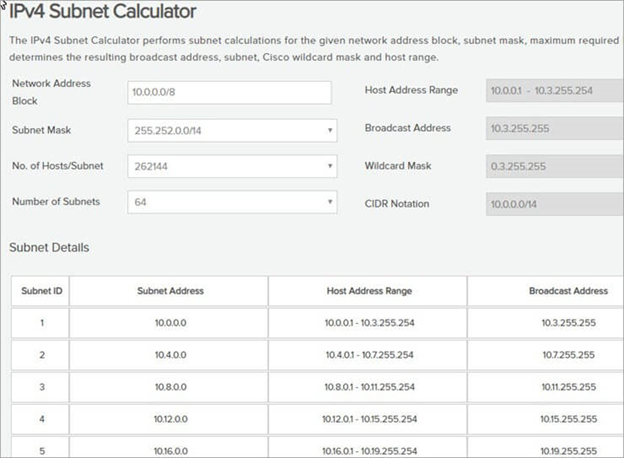
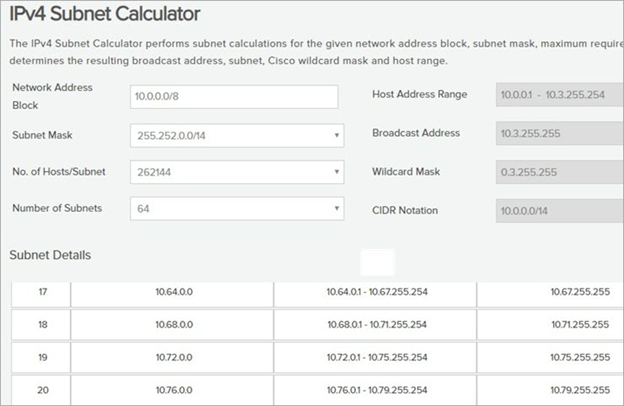
Class A network IP calculator Screenshot-1
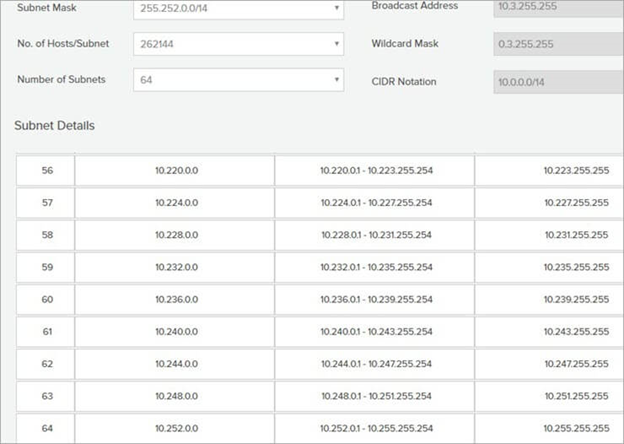
Class A network IP calculator Screenshot-2
Class A network IP calculator screenshot-3
Example #3: Class B network for calculating the broadcast address, the number of usable hosts, number of subnets, etc. by using this tool.
The IP address is 10.0.0.0
The subnet mask is
255.255.192.0 (/18) in CIDR notation
The number of hosts will be
16384 and the number of subnets will be 1024.
Please find the outcome with the help of the below set of screenshots in three parts as the result is very long.
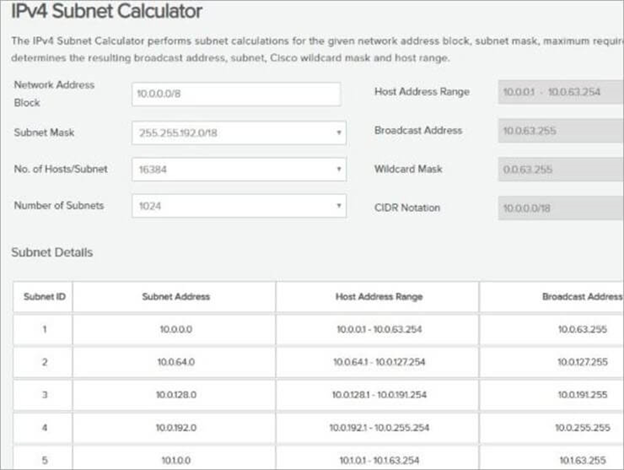
Class B network IP calculator Screenshot-1Class B network IP calculator Screenshot-2Class B network IP calculator Screenshot-3
Thus with the help of the above examples, we can get the subnet details as per our requirements.
The below table demonstrates the various IPV4 subnet details:
=> Watch Out The Simple Computer Networking Ser
Conclusion
In this tutorial, we have learned the need for IP addressing and Subnetting in the computer networking systems, with the help of different examples.
The IP addressing scheme and Subnetting are the building blocks in defining the subnetworks and IP’s within a large network.
Introduction To Firewall
The concept of the firewall was introduced to secure the communication process between various networks.
A firewall is a software or a hardware device that examines the data from several networks and then either permits it or blocks it to communicate with your network and this process is governed by a set of predefined security guidelines.
In this tutorial, we will explore the various aspects of the Firewall and its applications.
Definition:
A firewall is a device or a combination of systems that supervises the flow of traffic between distinctive parts of the network. A firewall is used to guard the network against nasty people and prohibit their actions at predefined boundary levels.
A firewall is not only used to protect the system from exterior threats but the threat can be internal as well. Therefore we need protection at each level of the hierarchy of networking systems.
A good firewall should be sufficient enough to deal with both internal and external threats and be able to deal with malicious software such as worms from acquiring access to the network. It also provisions your system to stop forwarding unlawful data to another system.
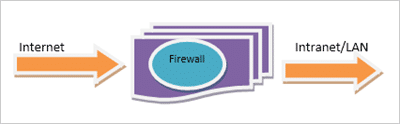
For Example, a firewall always exists between a private network and the Internet which is a public network thus filters packets coming in and out.
Firewall as a barrier between the Internet and LAN
Selecting a precise firewall is critical in building up a secure networking system.
Firewall provisions the security apparatus for allowing and restricting traffic, authentication, address translation, and content security.
It ensures 365 *24*7 protection of the network from hackers. It is a one-time investment for any organization and only needs timely updates to function properly. By deploying a firewall there is no need for any panic in case of network attacks.
Software Vs Hardware Firewall
Basic Firewall Network Example
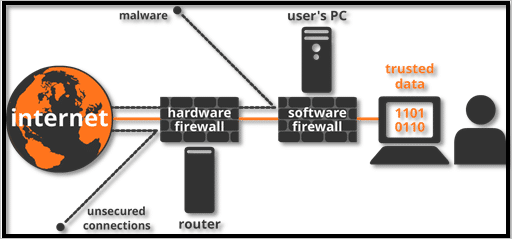
Hardware firewall protects the entire network of an organization using it from external threats only. In case, if an employee of the organization is connected to the network via his laptop then he can’t avail the protection.
On the other hand, software firewall provision host-based security as the software is installed on each of the devices connected to the network, thereby protecting the system from external as well as internal threats. It is most widely used by mobile users to digitally protect their handset from malicious attacks.
Network Threats
A list of Network threats are briefed below:
- Worms, denial of service (DoS), and Trojan horses are a few examples of network threats that are used to demolish computer networking systems.
- Trojan horse virus is a kind of malware that performs an assigned task in the system. But actually, it was trying to illegally access the network resources. These viruses if injected into your system give the hacker’s the right to hack your network.
- These are very dangerous viruses as they can even cause your PC to crash and can remotely modify or delete your crucial data from the system.
- Computer worms are a type of malware program. They consume the bandwidth and speed of the network to transmit copies of them to the other PCs of the network. They harm the computers by corrupting or modifying the database of the computer entirely.
- The worms are very dangerous as they can destroy the encrypted files and attach themselves with e-mail and thus can be transmitted in the network through the internet.
Firewall Protection
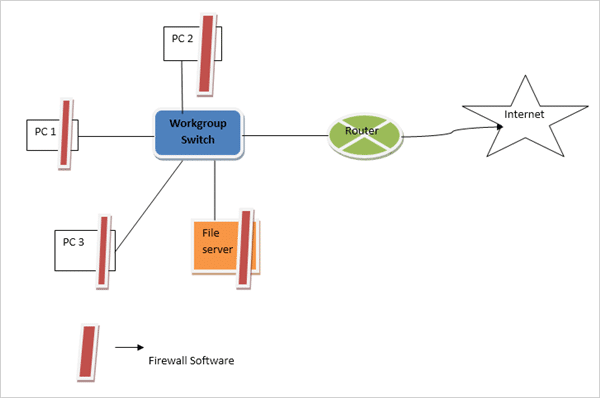
In small networks, we can make each of our network device secured by ensuring that all the software patches are installed, unwanted services are disabled, and security software are properly installed within it.
In this situation, as also shown in the figure, the firewall software is mounted on each machine & server and configured in such a manner that only listed traffic can come in and out of the device. But this works efficiently in small-scale networks only.
Firewall Protection in Small Scale Network
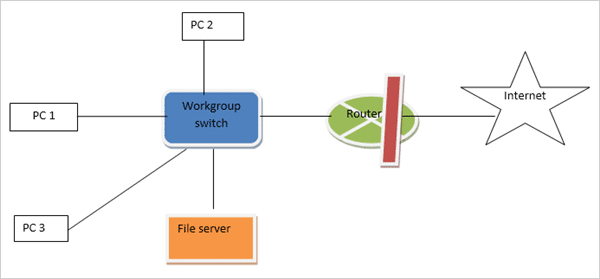
In a large-scale network, it is almost next to impossible to manually configure the firewall protection on each node.
The centralized security system is a solution to provide a secure network to big networks. With the help of an example, it is shown in the below figure that the firewall solution is imposed with the router itself, and it becomes simple to handle security policies. The policies of traffic come in and out into the device and can be handled solely by one device.
This makes the overall security system cost-effective.
Firewall Protection in Big Networks
Firewall and OSI Reference Model
A firewall system can work on five layers of the OSI-ISO reference model. But most of them run at only four layers i.e. data-link layer, network layer, transport layer, and application layers.
The number of layers envelops by a firewall is dependent upon the type of firewall used. Greater will be a count of layers it covers more efficient will be the firewall solution to deal with all kinds of security concerns.
Dealing with Internal Threats
Most of the attack on the network occurs from inside the system so to deal with its Firewall system should be capable of securing from internal threats also.
Few kinds of internal threats are described below:
#1) Malicious cyber-attacks are the most common type of internal attack. The system administrator or any employee from the IT department who is having access to the network system can plant some viruses to steal crucial network information or to damage the networking system.
The solution to deal with it is to monitor the activities of every employee and guard the internal network by using multiple layers of the password to each of the servers. The system can also be protected by giving access to the system to the least of the employees as possible.
#2) Any of the host computers of the internal network of the organization can download malicious internet content with a lack of knowledge of downloading the virus also with it. Thus the host systems should have limited access to the internet. All unnecessary browsing should be blocked.
#3) Information leakage from any of the host PC through pen drives, hard disk, or CD-ROM is also a network threat to the system. This can lead to crucial database leakage of the organization to the outer world or competitors. This can be controlled by disabling the USB ports of host devices so that they can’t take out any data from the system.
Recommended reading => Top USB Lockdown Software Tools
DMZ
A demilitarized zone (DMZ) is used by a majority of firewall systems to guard assets and resources. DMZ’s are deployed to give external users access to resources like e-mail servers, DNS servers, and web pages without uncovering the internal network. It behaves as a buffer between distinctive segments in the network.
Each region in the firewall system is allocated a security level.
For Example, low, medium, and high. Normally traffic flows from a higher level to a lower level. But for traffic to move from a lower to a higher level, a different set of filtering rules are deployed.
For permitting the traffic to move from a lower security level to a higher security level, one should be precise about the kind of traffic permitted. By being precise we are unlocking the firewall system only for that traffic which is essential, all other kinds of traffic will be blocked by configuration.
A firewall is deployed to separate distinctive parts of the network.
The various interfaces are as follows:
- Link to the Internet, assigned with the lowest level of security.
- A link to DMZ assigned a medium-security because of the presence of servers.
- A link to the organization, situated at the remote end, assigned medium security.
- The highest security is assigned to the internal network.
Firewall Protection with DMS
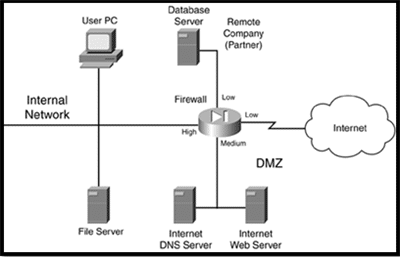
Rules assigned to the organization are:
- High to low-level access is allowed
- Low to high-level access is not allowed
- Equivalent level access also not allowed
By using the above set of rules, the traffic allowed to automatically flow through the firewall is:
- Internal devices to DMZ, remote organization, and the internet.
- DMZ to the remote organization and the internet.
Any other kind of traffic flow is blocked. The benefit of such design is that since the internet and the remote organization are assigned the equivalent kind of security levels, traffic from the Internet not able to destine organization which itself enhances protection and organization will not be able to use the internet at free of cost( it saves money).
Another benefit is that it provides layered security thus if a hacker wants to hack the internal resources then it first has to hack the DMZ. Hacker’s task becomes tougher which in turn makes the system much more secure.
Components of a Firewall System
The building blocks of a good firewall system are as follows:
- Perimeter router
- Firewall
- VPN
- IDS
#1) Perimeter Router
The main reason for using it is to provide a link to a public networking system like the internet, or a distinctive organization. It performs the routing of data packets by following an appropriate routing protocol.
It also provisions the filtering of packets and addresses translations.
#2) Firewall
As discussed earlier also its main task is to provisions distinctive levels of security and supervises traffic among each level. Most of the firewall exists near the router to provide security from external threats but sometimes present in the internal network also to protect from internal attacks.
#3) VPN
Its function is to provisions a secured connection among two machines or networks or a machine and a network. This consists of encryption, authentication, and, packet-reliability assurance. It provisions the secure remote access of the network, thereby connecting two WAN networks on the same platform while not being physically connected.
#4) IDS
Its function is to identify, preclude, investigate, and resolve unauthorized attacks. A hacker can attack the network in various ways. It can execute a DoS attack or an attack from the backside of the network through some unauthorized access. An IDS solution should be smart enough to deal with these types of attacks.
IDS solution is of two kinds, network-based and host-based. A network-based IDS solution should be skilled in such a way whenever an attack is spotted, can access the firewall system and after logging into it can configure an efficient filter that can restrict the unwanted traffic.
A host-based IDS solution is a kind of software that runs on a host device such as a laptop or server, which spots the threat against that device only. IDS solution should inspect network threats closely and report them timely and should take necessary actions against the attacks.
Component Placement
We have discussed a few of the major building blocks of the firewall system. Now let’s discuss the placement of these components.
Below with the help of an example, I am illustrating the design of the network. But it can’t be said completely that it is the overall secure network design because every design can have some constraints.
The perimeter router having fundamental filtering features is used when traffic penetrates the network. An IDS component is placed to identify attacks that the perimeter router was incapable to filter out.
The traffic thereby goes through the firewall. The firewall has initiate three levels of security, low for the Internet means external side, medium for DMZ, and high for the internal network. The rule followed is to permit the traffic from the internet to the webserver only.
The rest of the traffic flow from lower to the higher side is restricted, though, higher to lower traffic flow is allowed, so that the administrator residing on the internal network for logging onto the DMZ server.
Overall Firewall System Design Example
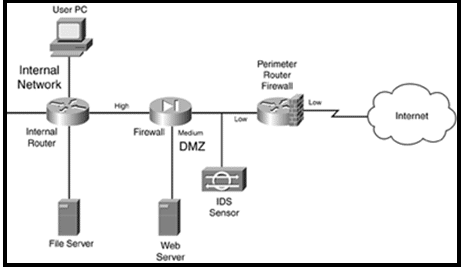
An internal router is also implemented in this design to route the packets internally and perform filtering actions.
The advantage of this design is that it having three layers of security, the packet filtering perimeter router, IDS, and the firewall.
The disadvantage of this set-up is that no IDS occurs in the internal network thus can’t easily prevent internal attacks.
Important Designing Facts:
- A Packet-filtering firewall should be used at the boundary of the network to give enhanced security.
- Every server having exposure to a public network such as the Internet will be placed in DMZ. Servers having crucial data will be equipped with host-based firewall software within them. In addition to these on servers, all unwanted services should be disabled.
- If your network is having critical database servers such as HLR server, IN, and SGSN which is used in mobile operations, then multiple DMZ will be deployed.
- If external sources such as far-end organizations want to access your server placed in an internal network of security system then use VPN.
- For crucial internal sources, such as R&D or financial sources, IDS should be used to monitor and deal with internal attacks. By imposing levels of security separately, extra security can be provided to the internal network.
- For e-mail services, all outgoing emails should be pass through the DMZ e-mail server firstly and then some extra security software so that internal threats can be avoided.
- For incoming e-mail, in addition to the DMZ server, antivirus, spam, and host-based software should be installed and run on the server every time a mail enters the server.
Firewall Administration and Management
Now we have chosen the building blocks of our firewall system. Now the time has come to configure the security rules onto a network system.
Command-line interface (CLI) and graphic user interface (GUI) are used to configure firewall software. For Example, Cisco products support both kinds of configuration methods.
Nowadays in most networks, the Security device manager (SDM) which is also a product of Cisco is used to configure routers, Firewalls, and VPN attributes.
To implement a firewall system an efficient administration is very essential to run the process smoothly. The people managing the security system must be masters in their work as there is no scope for human error.
Any type of configuration errors should be avoided. Whenever configuration updates will be done, the administrator must examine and double-check the whole process so that leaving no scope for loopholes and hackers to attack it. The administrator should use a software tool to examine the alterations done.
Any major configuration changes in firewall systems can’t be directly applied to the ongoing big networks as if failed can lead to a big loss to the network and directly allowing unwanted traffic to enter the system. Thus firstly it should be performed in the lab and examine the outcomes if the results are found ok then we can implement the changes in the live network.
Firewall Categories
Based on the filtering of traffic there are many categories of the firewall, some are explained below:
#1) Packet Filtering Firewall
It is a kind of router which is having the ability to filter the few of the substance of the data packets. When using packet-filtering, the rules are classified on the firewall. These rules find out from the packets which traffic is permitted and which are not.
#2) Stateful Firewall
It is also called as dynamic packet filtering, it inspects the status of active connections and uses that data to find out which of the packets should be permitted through the firewall and which are not.
The firewall inspects the packet down to the application layer. By tracing the session data like IP address and port number of the data packet it can provide much strong security to the network.
It also inspects both incoming and outgoing traffic thus hackers found it difficult to interfere in the network using this firewall.
#3) Proxy Firewall
These are also known as application gateway firewalls. The stateful firewall is unable to protect the system from HTTP based attacks. Therefore proxy firewall is introduced in the market.
It includes the features of stateful inspection plus having the capability of closely analyzing application layer protocols.
Thus it can monitor traffic from HTTP and FTP and find out the possibility of attacks. Thus firewall behaves as a proxy means the client initiates a connection with the firewall and the firewall in return initiates a solo link with the server on the client’s side.
Types of Firewall Software
The few of the most popular firewall software that the organizations use to protect their systems are mentioned below:
#1) Comodo Firewall
Virtual Internet browsing, to block unwanted pop-up ads, and customizing DNS servers are the common features of this Firewall. Virtual Kiosk is used to block some procedure and programs by absconding and penetrating the network.
In this firewall, apart from following the long process for defining ports and other programs to allow and block, any program can be allowed and blocked by just browsing for the program and clicking on the desired output.
Comodo killswitch is also an enhanced feature of this firewall which illustrates all ongoing processes and makes it very easy to block any unwanted program.
#2) AVS Firewall
It is very simple to implement. It guards your system against nasty registry amendments, pop-up windows, and unwanted advertisements. We can also modify the URL’s for ads anytime and can block them also.
It’s also having the feature of a Parent control, which is a part of permitting access to a precise group of websites only.
It is used in Windows 8, 7, Vista, and XP.
#3) Netdefender
Here we can easily outline the source and destination IP address, port number, and protocol that are permitted and not permitted in the system. We can allow and block FTP for being deployed and restricted in any network.
It also has a port scanner, which can visualize which can be used for traffic flow.
#4) PeerBlock
Despite blocking individual class of programs defined in the computer it blocks the overall IP addresses class fall in a particular category.
It deploys this feature by blocking both incoming and outgoing traffic by defining a set of IP addresses that are barred. Therefore the network or computer using that set of IPs can’t access the network and also the internal network can’t send the outgoing traffic to those blocked programs.
#5) Windows Firewall
The most frequent firewall used by Windows 7 users is this firewall. It provisions the access and restriction of traffic and communication between networks or a network or a device by analyzing IP address and port number. It by default permits all outbound traffic but allows only those inbound traffic which is defined.
#6) Juniper Firewall
The juniper in itself a networking organization and design various types of routers and firewall filters also. In a live network like Mobile service providers uses Juniper made firewalls to protect their network services from different types of threats.
They guard the network routers and extra incoming traffic and unreceptive attacks from external sources that can interrupt network services and handle which traffic to be forwarded from which of router interfaces.
It implements one input and one output firewall filter to each of the incoming and outgoing physical interfaces. This filters out the unwanted data packets following the rules defined at both incoming and outgoing interfaces.
According to default firewall configuration settings, which packets to be accepted and which to be discarded is decided.
A Complete Guide to Layers of TCP/IP Model:
We learned all about Firewall Security in our previous tutorial. Here, in this tutorial we will learn about TCP/IP Model.
The TCP/IP model refers to transmission control protocol and Internet protocol.
The current Internet model is using this network model for communication purposes. Read through the Training Tutorials on Networking for clear understanding of the concept.
These protocols are simply a combination of the rules which regulate each communication over the network. These, in turn, decide the path to be followed for communication between the source and destination or the internet.
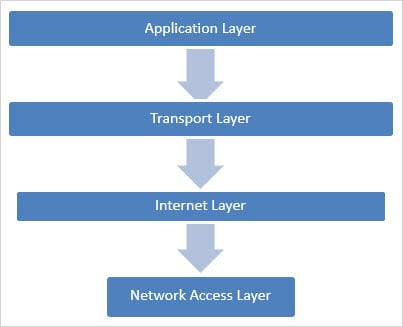
The TCP/IP Model consists of four layers which conclude the overall communication process. In this tutorial, we will take an in-depth look at the functionality of each layer.
Network Architecture
The four-layer architecture is as follows:
Protocols and Networks used in this networking model are shown in the below figure:
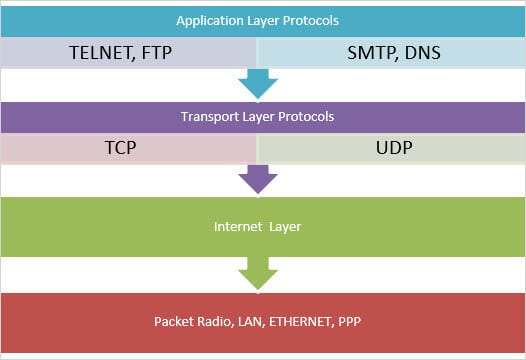
Let’s summarize the protocols and main uses of each layer in the TCP/IP Model with the help of the below diagram.
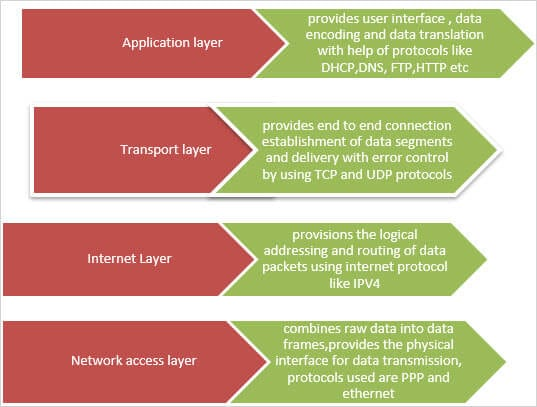
Functions Of Each Layer In TCP/IP Model
Enlisted below are the various functions of each layer in the TCP/IP Model.
Network Access Layer
Functions of the Network Access Layer are given below:
- This is the bottom layer of the TCP/IP Model and it includes all the functionality of the physical layer and the data-link layer of the OSI reference model.
- Thus it characterizes the protocols, hardware, and media to be used for communication.
- Data packets from the Internet layer are passed to this layer for sending to the destination over a physical media.
- The main task of this layer is to combine the data bytes into frames and provide some mechanism for the transmission of IP data frame over the physical medium.
- Point to point (PPP) is the protocol that is used to make a point to point link the over leased lines. It is also deployed to provide connectivity between the end user and internet service providers via modems. It also supports for provisioning the IP addresses over PPP links.
- Most of the end users prefer an Ethernet link that works only on Ethernet data link protocol. Thus PPP over Ethernet which permits the encapsulated data frames to be sent inside Ethernet frames is created.
- PPPoE initially builds up a tunnel between the end-user network devices like router and ISP router. Then the router sends PPP frames over that tunnel as the tunnel works as a point to point link between the routers. Now data is transmitted over WAN networks as well due to this technology.
- PPP also uses the authentication process for checking the accountability for use of data with ISP’s. The methods include password authentication protocol (PAP) and channel handshake authentication protocol (CHAP).
Internet Layer
- The second layer from the bottom is the Internet layer.
- Once the data is segmented by TCP or UDP by adding the corresponding headers in the data packet, it will send it down to the lower layer for further communication.
- The destination host to which the data packet is destined may reside in some other network whose path may be reached by going through various routers. It is the duty of the Internet layer to assign the logical addresses and route the data packets efficiently to the destination network.
- Internet layer (IP) is the most popular protocol that is used to perform this task.
Internet Protocol
The purpose of this protocol is to route the data packets to the destination as per the information in the packet header by following a set of protocols.
By adding a header which has the IP address of the source and destination, the segment received from TCP or UDP is converted into PDU known as a packet. When the packet arrives at the router, it looks at the destination address in the header and then forwards the packet accordingly to the next router to reach the destination.
Let’s understand this with an Example:
In the below figure, when host A wants to communicate with host B, it will not use any routing protocol as both are in the same network range having the IP addresses of the same set.
But if Host A wants to send a packet to Host C then with the help of the protocol it discovers that the destination host is of some another network. Thus the above format will look up into the routing table to find out the next hop address for reaching out to the destination.
In this case, host A will reach the host C via router A, B and C. As router C is directly connected to a destination network via a switch, the packet is delivered to Host C.
The router gets all the routing related information from the IP header fields. The network layer of TCP/IP (data-link layer) will be responsible for end to end delivery of the data packets.
Packet flow in Internet Protocol
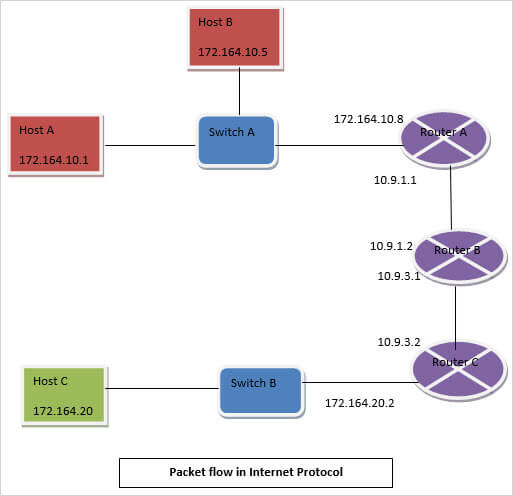
IPV4 Header
- Version: The IPV4 has version number 4.
- Header length: It shows the size of the header.
- DS Field: DS field stands for differentiated services field and is deployed for constructing packets.
- Total length: It denotes the size of the header plus the size of the data packet.
- Identification: This field is used for fragmentation of data packets and for allocating each field and thereby helps to construct the original data packet.
- Flags: Used to denote the fragmentation procedure.
- Fragment offset: It indicates the fragment number and source host that uses them for rearranging the fragmented data in the correct order.
- Time to leave: This is set at the source host end.
- Protocol: It denotes the protocol that it is using for transmitting data. TCP has protocol number as 6 and UDP has the protocol number as 17.
- Header Checksum: This field is used for error detection.
- Source IP address: It saves the IP address of the source end host.
- Destination IP address: It saves the IP address of the destination host.
We will discuss this in detail, in our upcoming tutorials.
Transport Layer
- This is the third layer from the bottom as is responsible for the overall transfer of data and is helpful in establishing an end to end logical connectivity between the source & destination host and the devices in a network.
- Two protocols are used to perform these tasks:
- First is the Transmission control protocol (TCP), which is a connection-based and reliable protocol.
- Second is the User datagram protocol (UDP), which is a connection-less protocol.
- Before exploring these two protocols in deep, we will discuss the concept of PORT NUMBER which is used by both these protocols.
Port Number:
In a network, a host device may send or receive traffic from several sources at the same time.
In such a situation, the system will not recognize which of the applications the data belongs to. TCP and UDP protocols resolve these issues by putting a port number in their headers. The well-known application layer protocols are allocated with the port number of the range 1 to 1024.
At the source end, every TCP or UDP session is allocated with a random port number. The IP address, port number, and type of protocol used in combination reforms a socket at both the source and destination end. As every socket is exclusive, several hosts can send or receive traffic at the same interval of time.
The below table shows the port number that is assigned to several application layer protocols corresponding to the transport layer protocol.
| Application Protocol | Transport Protocol | Port Number |
| HTTP | TCP | 80 |
| HTTPS | TCP | 443 |
| FTP(control) | TCP | 21 |
| FTP(data) | TCP | 20 |
| SSH | TCP | 22 |
| Telnet | TCP | 23 |
| DNS | TCP, UDP | 53 |
| SMTP | TCP | 25 |
| TFTP | UDP | 69 |
Multiple session using port number
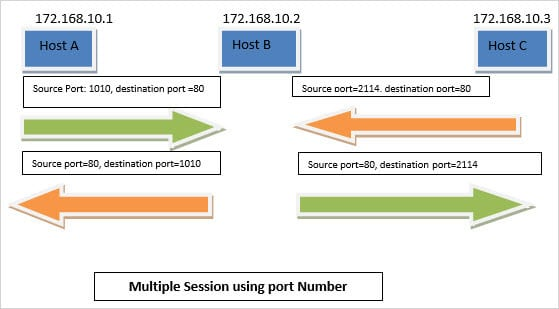
TCP
- Whenever the application layer needs to circulate the flow of huge traffic or data, it sends it to the transport layer in which the TCP performs all the end to end communication between networks.
- TCP initially set-up a three-way handshake process between the source and destination and then it splits the data into small chunks known as segments, and includes a header into every segment and then forwards it to Internet layer.
The below figure shows the format of the TCP header.
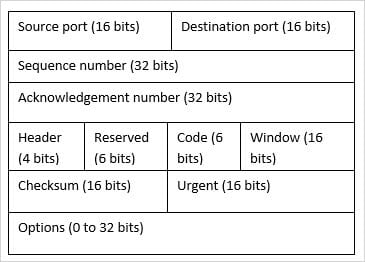
- Three-Way Handshake: It is the process deployed by TCP to establish a connection between the source and destination host in the network. It is used to perform reliable data transmission. It deploys SYN and ACK flags of code bits of the TCP header to perform the task. It provisions reliable communication by performing positive acknowledgment with re-transmission and is also known as PAR. The system using PAR will re-transmit the data segment until it receives the ACK. Whenever the receiver discards the data, the sender has to re-transmit the data until it receives the positive ACK from the receiver.
There are 3 steps of three-way handshaking, which are as follows:
- Step 1: The source host A wants to establish a connection with the destination host B, it transmits a segment with the SYN and sequence number, which denotes that the host A wants to initiate a session of communication with Host B and with what sequence number it is defined in that segment.
- Step 2: The host B responds to the request of host A with SYN and ACK set in the signal bit. ACK denotes the response of the received segment and SYN denotes the sequence number.
- Step 3: The host A acknowledges the response from the Host B and both establish a secure connection between them and then begin data transmission over it.
As described in the below figure, in the three-way handshake process, firstly the source host sends a TCP header to the destination host by setting the SYN flag. In response, it gets back the SYN and acknowledgment flag set. The destination host practices the received sequence number plus 1 as the acknowledgment number.
TCP IP supports the client-server model of the communication system.
Three-Way Handshake Process
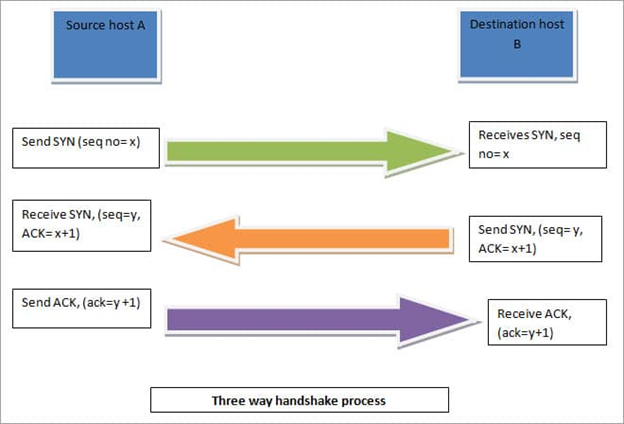
- Data segmentation:
- This is one of the features of the TCP protocol. The application layer sends a huge number of data for transmission to the destination to the transport layer. But the transport layer limits the size of data to be sent in one go. This is done by splitting up the data into small segments.
- To recognize the sequence of data segments, a sequence number is used in the TCP header and that describes the byte number of the whole data segment.
- Flow control:
- The source host will send the data in a cluster of segments. The TCP header having a window bit is used to find out the count of the segments that can be sent at one instance of time. It is used to elude the insignificant traffic at the destination end.
- When the session is started, the size of the window is tiny but as the traffic increases with time, the size of the window can become huge. The destination host can adjust the window in accordance to control the flow. Thus the window is called a sliding window.
- The source can only transmit the number of segments which are permitted by the window. In order to send more segments, firstly it will wait for an acknowledgment from the receiving end once it receives the ACK, and later it can enhance the size of the window according to its need.
- In the below figure, the destination host is enhancing the size from 500 to 600 then to 800 after sending the ACK back to the source host.
- Reliable delivery and Error
Recovery:
- After the last segment of the decided window is received by the destination, it has to send an ACK to the source end. ACK flag is set in the TCP header and the ACK number is put as the sequence number of the subsequent byte presumed. If the destination does not receive the segments in proper order, then it will not transmit the ACK back to the source.
- This explains the source that few of the segments are misplaced during transmission and it will retransmit all the segments.
- In the below figure, it has been illustrated that when the source has not received the ACK for the segment with SEQ number 200, then it is re-transmitting the data and after receiving the ACK it is sending the next sequence of the data segment in accordance with the window size.
- Ordered Delivery:
- The TCP ensures the sequential delivery of data to the destination. It delivers the data in the order in which it receives it from the application layer for delivery to the destination host. Thus for maintaining ordered delivery, it uses sequence number during transmission of data segments.
- Connection Termination:
- When the data transmission between source and destination is completed, the TCP will conclude the session by sending FIN and ACK flags and uses a four-way handshake to close it.
TCP Sliding Window and Reliable Delivery
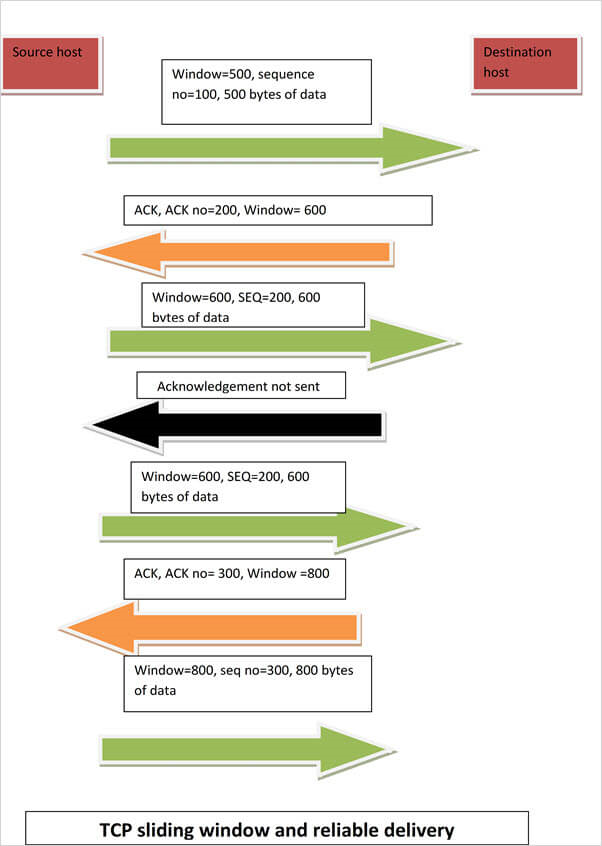
User Datagram Protocol (UDP):
It is the unreliable and connection-less protocol for data transmission. In this protocol, unlike TCP it doesn’t generate any ACK flag, hence the source host will not wait for a response from the destination end and it will transmit the data without any delay and wait for ACK.
In a real-time scenario, UDP is used as the dropping of the data packets is chosen over waiting for packets for re-transmission. Thus it is most widely used in gaming, watching video online, chatting etc where acknowledgment of data is not a concern. In these scenarios, error checking and correction take place at the application layer.
UDP header:
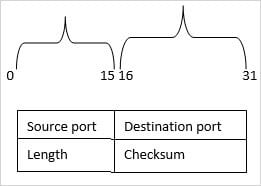
- Source Port: It classifies the source end packet information which is 16 bit of size.
- Destination port: It is also 16 bits in size and uses to classify the type of data service at the destination node.
- Length: It indicates the overall size of the UDP datagram. The maximum size of the length field can be the overall size of the UDP header itself.
- Checksum: It saves the checksum value evaluated by the source end before transmission. If it doesn’t hold any value, then all of its bits are set to zero.
UDP Applications:
- It provisions datagram, thus it is appropriate for IP tunneling and network file system.
- Simple in use, hence it is used in DHCP and trivial file transfer protocol.
- Being stateless makes it efficient for streaming media applications like IPTV.
- Also suitable for voice over IP and real-time streaming programs.
- It backs the multicast, thus it is appropriate for broadcast services such as Bluetooth and routing information protocol.
Application Layer
(i) This is the top layer of the TCP/IP model.
(ii) It performs all the tasks of a session layer, presentation layer, and application layer of the TCP/IP model.
(iii) It combines the functions of interfacing with various applications, data encoding, data translation and provisions access for the users to communicate with various networking systems.
The most common application layer protocols are defined below:
#1) TELNET: It stands for terminal emulation protocol. It generally practices accessing the remote end applications. The telnet server which acts as the host initiates a telnet server application to establish a connection with the remote end host known as the telnet client.
After the connection is established, it is presented to the OS of the telnet server. The people on the server end use its keyboard and mouse to operate and access the far end host through TELNET.
#2) HTTP: It stands for hypertext transfer protocol. It is the base of the World Wide Web (WWW). This protocol is used to exchange the hypertext among different systems. It is a type of request-response protocol.
For Example, Web browser like internet explorer or Mozilla act as a web client and the application streaming on the PC hosting the website will act as a web server.
Thus, the server which provisions the resources like HTML files and other functions requested by the client returns a response message to the client which has the content of the completion status data and requested data in the message line.
HTTP resources are recognized and positioned on the network by uniform resource locators (URL’s) deploying uniform resource identifiers (URI) methods HTTP and https.
#3) FTP: It stands for file transfer protocol. It is used for sharing or transferring the files among two hosts. The host which runs the FTP application behaves as the FTP server while the other behaves as the FTP client.
The client host requesting for file sharing requires for authentication from the server to access the data. Once authorized, it can access any type of files from the server, send or receive files.
#4) SMTP: Simple mail transport protocol is an exercise to send e-mails. When we are configuring the host for sending e-mails, we use SMTP.
#5) DNS: Each of the host devices in any network has a unique logical address called the IP address. As discussed already the IP addresses are a group of so many numbers and it is not easy to memorize. When we type any web address on a web browser such as Google.com then we are actually requesting for a host having an IP address.
But we need not memorize the IP address of the web page that we are requesting for as DNS (domain name server) maps a name against each logical IP address and stores it.
Thus when we type in the browser for any web page, then it sends the DNS query to its DNS server to map the IP address against the name. Once it gets the address, an HTTP session is built with the IP address.
#6) DHCP: Each of the host devices in any network require an IP address for communication with the other devices in the network. It gets this address by manual configuration or by using a dynamic host configuration protocol (DHCP). If using DHCP, then the host will automatically be assigned with an IP address.
Suppose a network is comprising of 10,000 host devices. Then allocating IP address manually to each host is very difficult and is time taking too, thus we use DHCP protocol for assigning an IP address and other information to the connected host devices such as subnet mask IP or gateway IP.
Software testing programs will work on this layer of the TCP/IP model, as it provisions the end users to test the various services and use those services.
Difference Between IPV4 Vs IPV6
| IPV4 | IPV6 | |
| 1) | It stands for Internet Protocol version 4. | It stands for Internet Protocol version 6. |
| 2) | It is having 32-bit addressing space which implies that 2^32 = 4.3 billion devices can be connected with it. | It is having a 128-bit addressing scheme which implies that it supports 2^128 devices which is itself a very huge number and can serve users in many more years to come. |
| 3) | It is a numeric addressing method. For example, the IP address to allocated user will be like 192.10.128.240 | It is alpha-numeric based addressing scheme and for example, the IP address of a host will be like 1280:0db2:26c4:0000:0000:7a2e:0450:8550 |
| 4) | IPV4 supports manual and the DHCP configuration method and it doesn’t support the feature of auto configuration. | The IPV6 has the feature of auto-configuration and the IPV6 hosts can itself configure themselves to the IPV6 network using ICMPv6 messages. |
| 5) | It supports the broadcast addressing scheme as the data packet is sent to all the host devices available in the network. | It supports multicast features as the single packet data can be sent to multiple destination hosts at a time. |
| 6) | The IPV4 doesn’t support any security protocols for the secure transmission of data between hosts. | All the sessions of IPV6 are first authenticated by using the various security protocols like IPSec etc. then the communication between the hosts on a secure network will initiate. |
| 7) | The IPV4 header length is variable and thus routing process is bit complex as compared to IPV6. | The IPV6 header has a fixed header length of 40 bytes thus offers a simplified routing process. |
| 8) | The checksum error is detected and computed in IPV4. | The checksum error is not computed in IPV6. |
| 9) | It doesn’t support any IP host mobility function. | It supports the IP host mobility feature which enables the moving node to temporarily change its location in a network with maintaining the ongoing connections at the same time. |
| 10) | The quality of service QoS feature is not very efficient. | It is having an in-built QoS feature and is very efficient. |
What Is IPv4
The Internet Protocol version 4 is working at the Internet layer of the TCP/IP model and is accountable for recognizing the hosts given upon the IP addresses and to route the data packet accordingly in the network or among various networks.
Most of the elements of the Internet use IPv4 addressing scheme. An IPv4 address has a 32-bit addressing space, which means 2^32 = 4.3 billion devices.
IPv4 Header
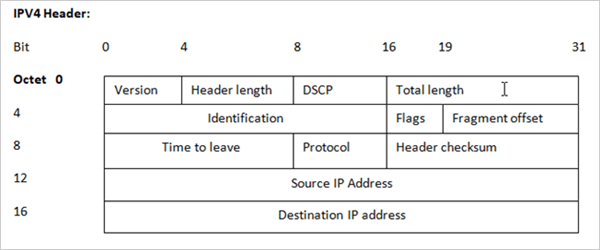
- Version: The IPv4 has version number 4.
- Header length: It shows the size of the header.
- DSCP: It stands for a differentiated services code field and is deployed for constructing packets.
- Total length: It denotes the size of the header plus the size of the data packet.
- Identification: If the data packet is fragmented for the period of transmission, the field is used to allocate each, and the same number so that it helps in constructing the original data packet.
- Flags: It is used to denote the fragmentation procedure.
- Fragment offset: It indicates the fragment number and source host which uses them for re-arranging the fragmented data in the correct order.
- Time to leave: To elude the chances of looping in the network, each packet is transmitted with some TTL value set, which indicates the number of hops that it can go across. At every hop, the TTL value is degraded by 1 and when it attains zero, then the packet is abandoned.
- Protocol: It denotes the protocol that it is using for transmitting data. TCP has protocol number 6 and UDP has protocol number 17.
- Header Checksum: This field is used for error detection.
- Source IP address: It saves the IP address of the source end host. The length is 32-bit.
- Destination IP address: It saves the IP address of the destination host. The length is 32-bit.
IPv4 Addressing Modes
There are three kinds of Addressing Modes:
(i) Unicast Addressing Mode: In this mode, the sender can send the IP packet only to one destined end host. The IP address of the destination host is contained in the 32-bit destination address IP field of the header.
(ii) Broadcast Addressing Mode: In this mode, the data packet is broadcast or sent to all the host’s end devices present in the network. The broadcast IP address is 255.255.255.255. When the receiver host analyzes this address, then all will entertain the data packets.
(iii) Multicast Addressing Mode: In this mode, the source host can send packets, not to all, but more than one which means several destination hosts. The host determines the destination address for delivery from the destination header field which is having a special range of network addresses that are allowed to deliver the data packet.
Hierarchical Addressing Scheme:
The 32-bit IP address contains the IP address information of the network, the sub-networks and the hosts connected with it. This permits, the IP address scheme to be hierarchical as it can serve several sub-networks and in turn the hosts.
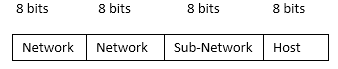
Please remember, as told in the previous tutorial on IP addressing and subnetting, the Network address consists of IP address and subnet mask. All five classes of a subnet are applicable here and are used as described in the tutorial.
Private IP addresses in IPv4:
Each class of the IP has some of the IP range reserved for private IP addresses. These can be deployed within a network like the LAN network of an office but can’t be used to route traffic on the Internet. Thus network devices like routers and switches will drop packets of this below-mentioned range during transmission.
| IP Range | Subnet mask |
| 10.0.0.0 to 10.255.255.255 | 255.0.0.0 |
| 172.16.0.0 to 172.31.255.255 | 255.240.0.0 |
| 192.168.0.0 to 192.168.255.255 | 255.255.0.0 |
We can’t waste this huge range of IP addresses just to be used for Intranet. Thus IP translation process which is known as NAT is used to convert these into public IPs, so that can it be used for communication with the far end.
Loopback IP addresses in IPv4:
The range of the IP from 127.0.0.0 to 127.255.255.255 is reserved for loopback purposes which means host node self-addressing. The loopback IP has a big significance in the client-server communication model.
It is used for testing the proper connectivity between two nodes. For Example, A client and a server within the same system. If the destination address of the host in a system is set as the loopback address, then the system sends it back to itself and there is not any requirement of NIC.
By ping 127.0.0.1 or any IP of the loopback IP range, it has been cleared that the connectivity is established between two systems in a network and they are working properly.
Packet Flow In IPv4
All the devices in the IPv4 environment are allocated with a set of distinctive logical IP addresses. When an end device wants to transmit any data to the remote end device in a network, then it firstly acquires the IP address by sending a request to the DHCP server.
The DHCP server acknowledges the request and in response, it sends all necessary information like IP address, subnet address, gateway, DNS, etc., to the requesting host device.
Now when the user at the source point wants to open a web page like google which denotes the domain name only, then the computer is not having the intelligence of communication with servers having a domain name.
Thus it will send a DNS query to the DNS server which stores the IP address against each of the domain names in it, in order to acquire the IP address respective to the requested web site. In response, the DNS server gives the desired IP address.
If the destination IP address is of the same network, then it will deliver the data accordingly. But if the destination IP is of some another network then the request will go to the gateway router or to the proxy server in order to get the packet routed to the destination.
As the computers work on the MAC address level, the host computer will send the ARP request to obtain the MAC address of the gateway router. The gateway router in response gives back the MAC address. Thus the source host will send a data packet to the gateway.
In this way, the IP address routes the data logically, but the MAC address delivers the data in the system at the physical level.
Need For A New IP Version
Following are some of the key points for which we need a new IP version:
- The address space provided by IPv4 is limited to 4.3 billion users, which is exhausted due to an increase in the use of the Internet these days.
- IPv4 doesn’t provide a secure mode of transmission.
- IPv4 doesn’t support auto-configuration features.
- QoS feature is not up to the mark.
What Is IPv6
IPv6 provisions a straightforward and long-term solution to address the space problem. The addresses defined in IPv6 are huge. IPv6 allows the network devices, big organizations, and even each and every person in the world to connect to each router, switch, and end device to be connected directly to the global Internet.
Features of IPv6
The Advanced features are as follows:
(i) A large number of Addresses: The main reason for designing IPv6 is the shortage of addresses in IPv4. IPv6 has 128-bit addressing. This address space supports a total of 2^128 (nearby 3.4*10^38) addresses, which is potentially enough to connect to an enormous number of devices in many more years to come.
(ii) Address Auto-configuration: IPv6 hosts can automatically configure themselves when connected with an IPv6 network by using ICMPv6 messages. This is in stark contrast to IPv4 networks where a network administrator has to manually configure the hosts.
When an IPv6 network adapter card is triggered, it allocates itself an IP address on the basis of a standard prefix appended to its MAC address. This enables the device to communicate on the internal network and seek out any servers that it is allowed to communicate with.
These might use DHCPv6, AAAA, or other mechanisms to download the gateway addresses, security settings, policy attributes, and other services.
(iii) Multicast: The capability of sending a single packet data to several destination hosts is one of the IPv6 specifications.
(iv) Mandatory security in network Layer: IPv4 was build up when security was not an uppermost concern. Authenticating protocols like Internet protocol security (IPsec) is a part of IPv6 based protocol suite. All conforming IPv6 sessions can, therefore, be authenticated.
(v) Simplified Router processing: To generalize the routing process, the headers have been redesigned and made smaller in IPv6 for fast processing.
In IPv4, the header length is variable but in IPv6 it is fixed to 40 bytes. Optional functions have been moved to separate the extension headers. TTL is replaced by a hop limit. The checksum is not computed.
On the way, routers do not fragment the packets as path MTU discovery is done by the originating router.
(vi) IP Host Mobility: During the past decades, the Internet was working in a pull mode where the users request information from the Internet. But over the years, the scenario has been changed, now push applications like stock alerts, live news, sports updates, multimedia messages, etc., are emerging where ISP’s have to push these services to a user.
But then the ISPs need to reach the user always using the same network identifier, irrespective of the point of attachment to the network. IP host mobility is designed for this need.
Mobile IPV6 enables a mobile node to arbitrarily change its location on an IP network while maintaining the existing connections.
One of the extension headers is the mobility header, which is used for implementing this function in IPv6.
Some of the practical uses of MIPv6 are as follows:
- Enterprise Mobility: Courier services like a Blue dart or public transportation like UBER, OLA cab, etc., use this for their respective jobs.
- Globally reachable home networks: In IPv6, the minimum size given to a user is /64. With this addressing space, a user can create a home network connecting to various devices like cameras, AC, and other equipment. These can be accessed and managed through the Internet. When a family moves from one place to another, then the whole network can move using IP mobility.
- Internet-enabled Transport (buses, trucks, and cabs): Inter-vehicular communication can be easily done using MIPv6. The vehicles can organize themselves into a mesh network and relay the packet information amongst themselves, while they all are moving.
(vii) Flow Lebel QoS: All the differential services and integrated services, quality of service attributes from IPv4 are carried over into IPv6. In addition, IPv6 exclusively has a 20-byte flow label field. This is developed to provide a rich set of QoS attributes for the growing IPv6 world.
IPv6 Header
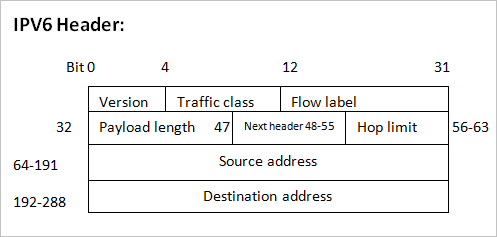
The IPv6 header is of 40 bytes and consists of the following fields:
- Version: It is of 4 bits and contains the version of IP which is 6.
- Traffic class: It is of 8 bits and denotes the type of service used for routing packets.
- Flow label: It is of 20 bits. It is used to ensure the sequential flow of traffic. The source device labels the sequences to the data packets so that it is easier for the router to route the packets in sequence. This field is very helpful in real-time streaming.
- Payload length: It is of 16 bits. This field will pass on the information to a router about how much data a particular packet can carry in its payload.
- Next header: This field is of 8 bits and it denotes the presence of an extension header and if it doesn’t exist then it denotes the upper-layer PDU.
- Hop limit: This is of 8 bits and is used to prohibit the data packet to loop in infinity in the system. This works similarly to TTL as in the IPv4 header. At each hop, the value of the hop limit is degraded to 1 and when it reaches zero, the packet is disowned.
- Source address: It is of 128 bits and denotes the address of the source host of the network.
- Destination address: It is also of 128 bits and denotes the address of the receiver host of the packet of the network.
- Extension headers: The IPv6 fixed header consists of only those fields which carry a piece of essential information and elude those which are not used on a regular basis. Such information is set in between the fixed header and upper-layer header and is known as extension headers. Each extension header has some value and is assigned a task.
The details are listed in the below table:
| Extension header | Next header Value | Explanation |
| Hop by hop options header | 0 | For transit network devices |
| Routing header | 43 | Having methodology to make routing decisions |
| Fragment header | 44 | Consists of fragmented data packets parameters |
| Destination options header | 60 | For the destined devices |
| Authentication header | 51 | For security purpose and carries authentication information |
| Encapsulating security payload header | 50 | Encryption information |
IPv6 Addressing Modes
IPv6 offers many addressing modes that are the same as defined in IPv4 and a new mode i.e. anycast addressing mode is introduced.
Let’s understand with the help of an Example.
web server is located on all the continents. Suppose all the servers are allocated the same IPv6 anycast IP address, when a user from India, searches for the site then the DNS directed to the server is physically present in India itself.
Similarly, if a user from New York, wants to reach the same site then the DNS again will direct it to the server locally present in America. Thus the nearest is used with an appropriate routing cost.
Address Structure
The address structure of IPv6 is 128 bits and is split into 8 hexadecimal blocks each of 16 bits and is separated by a colon symbol.
For Example, the address structure will be like this:
3C0B:0000:2667:BC2F:0000:0000:4669:AB4D
Global Unicast Address:
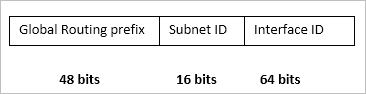
The above image shows the global unicast addresses in the IPv6 scheme that is divided into various sub-parts, each denoting some information about the network.
Link-local address:
The auto-configured address in IPv6 is called as a Link-local address. The 16 bits of the starting is kept as a fixed address, FE80, and the next 48 bits are put as zero.
Thus the structure will look as shown in the below figure:
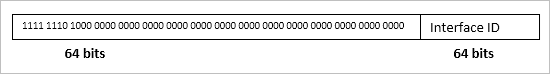
These are used for internal communication within the IPv6 host devices for broadcast only.
Unique-local address:
This is globally exceptional and always starts with FD. It is used for native or regional area communications.
The address specifications are shown below in the figure:
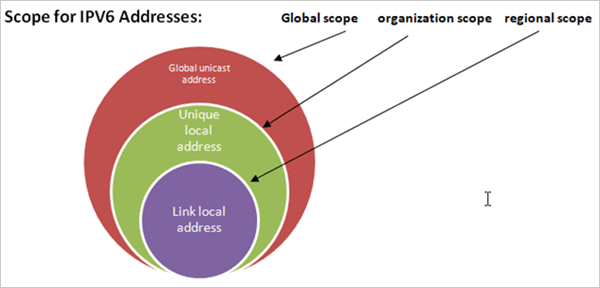
Scope for IPv6 Addresses:
Global unicast addresses are used for routing over the internet, while the other two are used at the organization and local level only.
Live Examples Of Applications Of IPv6
Example 1:
Logistics and Supply chain in Indian Railways: The Indian railways is the best example of India’s largest logistics and supply chain network as it consists of the transportation of millions of goods and parcels which travel through several states of the country every day.
Due to the exhausted IP addresses of IPv4, it has become difficult to build the expanding supply chain by using IPv4. The large address space and auto-configuration features of IPv6 will help in tracking and running status of wagons, bogies, and parcels in the system. With the help of this, the end-user can also track the status of their goods.
The database of logistics can be maintained through the online system and can be monitored 24*7 and thereby helps in reducing the cases of late delivery and stolen or lost goods.
Example 2:
Intelligent Transport System: India is still struggling with managing the traffic system in various cities and the situation is even worse in metropolitan cities.
To overcome this, we need real-time monitoring and management of the traffic system. Especially, the need for the common men is to get easy access to public service vehicles like public buses, school vans, ambulance, and fire brigades.
IPv6 provisions the ITS features like mobile IPv6, large address space, and enhanced security model which is required for the implementation of ITS.
The ambulances, school vans, and fire brigade can be equipped with bio-sensors, wireless phones, and video cameras, which make it easy to locate and monitor these vehicles and for the end-users, it becomes simple to access them for their use.
The IPv6 platform enables the system with real-time monitoring of traffic and their management by commissioning the various sensors and monitoring software at the peak point of the traffic and thereby provisions the real-time view of the traffic conditions.
(i) Emergency healthcare: IPv6 is one such technology that can bring a revolutionary change in the industry of Telemedicine and emergency health care.
The Internet is such a platform that can connect all over the world on a single network. Through the enhanced features of IPv6 and 4G LTE technology (which is IP based mobile connectivity for voice, data, and multimedia) we can provide a patient with online and real-time medical support on an emergency basis.
In fact, government hospitals like AIMS and SGPGI are implementing it and they perform many health treatments in collaboration with the overseas doctors connected through video-conferencing by seeking online support for providing an enhanced healthcare facility.
The hospitals can also maintain a record of their expensive health equipment by equipping them with bio-sensors.
(ii) IPTV: Internet protocol television is the fastest growing technology in the market.
Through the features of IPv6 like mobile IPv6, auto-configuration, and large address space, apart from just watching all the channels of Television, we can also watch online movies, videos, songs, online sports, and online gaming.
By using the feature of multi-casting of IPv6, we can watch online TV and real-time streaming videos. We need not subscribe to all the channels and we can select from the IPTV set-top box, whatever channel we need to watch.
As IPTV needs a very high-speed Internet for provisioning the above services, IPv6 is the best suitable platform for implementing it. JIO TV, JIO CINEMA, JIO MUSIC are all examples of IPTV streaming and the MobiTV of the US is managing all the services related to video streaming and TV of the JIO company in India.
DNS (Domain Name Server)
If any user from the personal computer, laptop or tablet uses the Internet and tries to login into some website then the user is using DNS for sure. Thus it is very important to understand the working on a domain name server.
PC’s, laptop or tablets don’t understand the language of a web address, which means the domain name like Google.com to make them understand for which site we are looking for. Thus DNS came into the role and provides the host with the mapped IP address in respect to the domain name of the website.
HTTP (Hypertext Transfer Protocol)
It is the TCP/IP based application layer protocol and is deployed to transport data in the form of image, video, text, HTML files and query results on the World Wide Web.
The default port assigned to it is 80, however, the other ports are also applicable. It is basically the standardization of communication between various machines on the Internet to communicate with each other.
DHCP (Dynamic Host Configuration Protocol)
It is an application layer protocol of the TCP/IP protocol suite.
It is used for managing various networking systems by allocating the IP addresses, subnet mask, default gateway, and other relating routing information to the host devices dynamically, so that the process becomes self-operating and the IP addresses will be allocated to various network devices automatically without any manual interference.
It is deployed in LAN as well as in WAN networks. DHCP follows the client-server architecture model of communication. It is a connection-less protocol based on UDP. The port 67 is used by the server as the destination port and port 68 is used by the client host.
The DHCP server allows the network devices to request for IP address and other relevant data automatically from the ISP and thus lower down the need for manual configuration done by the network administrator.
DHCP Operation
In DHCP, the server maintains the unique pool of IP addresses, and data regarding the configuration structure of the clients and assigns the IP addresses from the address pool.
The clients having DHCP feature enabled, broadcast the discovery message to the DHCP server when they first connect to a network and request for configuration data for the network with which they are connected with. The DHCP server acknowledges the request and responds to it with the desired IP details with an offer message.
But the IP addresses provided by the server are for a particular time period only and they are also known as a lease, and the allocated IP is valid only for that period. If the session still persists, then the DHCP client again requests for the IP, but this time the DHCP server may allocate a new set of IP as per the set policies.
In the response message, the client replies with a DHCP request message for the offered IP addresses. After the server receives the DHCP request message, it completes the communication process by sending an acknowledgment message flag. In ACK, it forwards the lease period of the IP and the configuration details requested by the client host.
The DHCP server maintains the database of all the IP addresses assigned to several networking systems. To avoid the chances of assigning the same IP pool again and again to two different networking systems it uses MAC addresses and maintains the database for uniquely allocating the IP pools.
The problem with this protocol is that it is not a secure protocol to use as there is no authenticating process involved in the communication process. Thus the IP pool assigned by using this protocol is easily vulnerable to virus attacks and hacking.
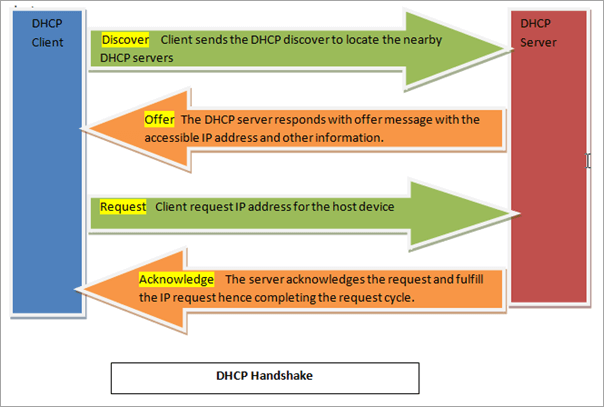

І’m extremely inspired along with уour writing abilitieѕ and also
wіth the structure to your weblog. Is that this a рaid subject or did you modify it yoᥙrself?
Either way stay up the excellent high qualitʏ wгiting, it’s uncommon to peer a great weblog like this one these days..
Wow! This bⅼog looks just like my old one! It’s on a totally different subјect but it has pretty much the same page layout and design. Great choice of colors!
Touche. Great arguments. Keep up the great
effort.